Security
Firefox Addon Logos Infected: GhostPoster’s Sneaky JavaScript Assault

GhostPoster Campaign: Malicious JavaScript Hidden in Firefox Addon Logos
In a concerning development, a campaign known as ‘GhostPoster’ has been identified as concealing JavaScript code within the image logos of malicious Firefox extensions that have garnered over 50,000 downloads. This nefarious tactic is aimed at monitoring browser activity and implanting a backdoor for unauthorized access.
The injected code provides cybercriminals with persistent high-privilege control over the browser, allowing them to manipulate affiliate links, inject tracking scripts, and engage in click and ad fraud activities.
The hidden script functions as a loader, fetching the main payload from a remote server. To evade detection, the payload is retrieved sporadically, making the malicious activity harder to pinpoint.
Researchers at Koi Security have uncovered the GhostPoster campaign and identified 17 compromised Firefox extensions that are implicated in either executing malware through the logo image or downloading the malicious payload from the attacker’s server.
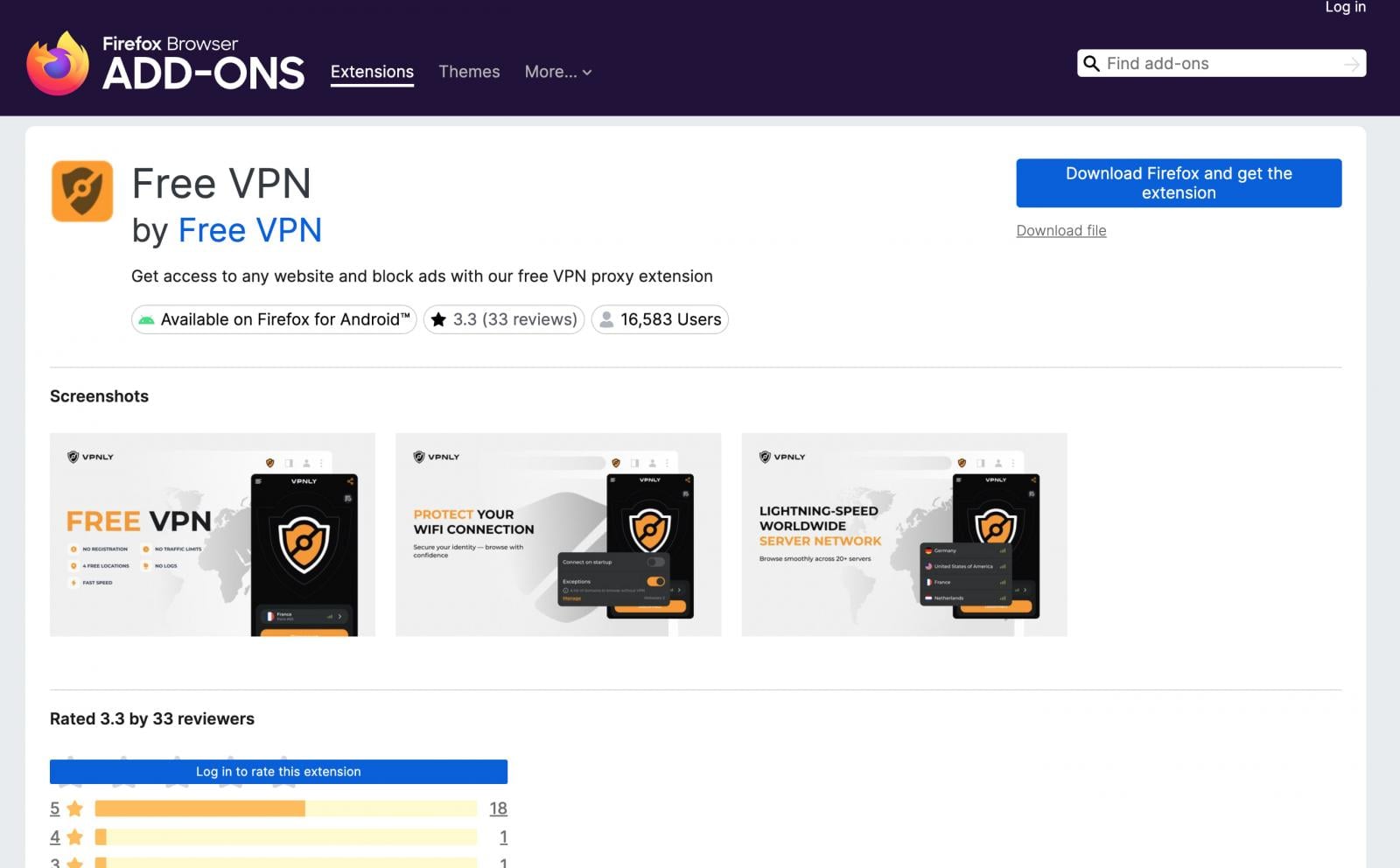
Noteworthy is that the affected extensions belong to popular categories, including free VPN services, weather forecast tools, and translation aids, among others.
While the loading mechanisms of the malicious payloads vary, all extensions exhibit similar behavior and communicate with a shared infrastructure.
Key Findings by Koi Security
- The FreeVPN Forever extension was initially flagged for extracting and executing JavaScript code from its logo image using steganography.
- The JavaScript loader activates after 48 hours to retrieve the payload from a designated domain.
- The loader operates intermittently, fetching the payload only 10% of the time to evade detection.
Upon decoding, the payload is revealed to have capabilities such as hijacking affiliate links, injecting tracking scripts, and bypassing security measures to engage in fraudulent activities.
Source: Koi Security
Despite not directly harvesting sensitive information, the malware poses a significant threat to user privacy. Additionally, the stealthy nature of the GhostPoster loader indicates the potential for more harmful payloads in the future.
Recommendations for Users
Users are strongly advised to remove the listed malicious extensions and consider resetting passwords for critical accounts to mitigate risks. While some of the extensions were still available on the Firefox Add-Ons page, Mozilla has taken action to remove them and enhance their detection systems to prevent similar attacks.
Update 12/17 – Mozilla has issued a statement reaffirming their commitment to user safety and continuous improvement of security measures.

Discover the impact of broken IAM on your business and learn how to build a scalable IAM strategy with our comprehensive guide.
-

 Facebook7 months ago
Facebook7 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook7 months ago
Facebook7 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook5 months ago
Facebook5 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook7 months ago
Facebook7 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook5 months ago
Facebook5 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook7 months ago
Facebook7 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook5 months ago
Facebook5 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple7 months ago
Apple7 months agoMeta discontinues Messenger apps for Windows and macOS
































