Security
BreachForums Hack: 324,000 Accounts Exposed

Breaking News Update: Additional details emerge in the aftermath of the BreachForums data breach.
In a significant development, the BreachForums hacking forum, known for facilitating the illicit trade, sale, and dissemination of stolen data, has once again fallen victim to a data breach, resulting in the exposure of its user database table on the internet.
Notorious for its involvement in cybercrime activities such as selling access to corporate networks and other illegal services, BreachForums has a long history of evading law enforcement crackdowns and reemerging under new domains.

The forum’s inception followed the closure of RaidForums, its predecessor, due to law enforcement intervention and the subsequent arrest of its owner, “Omnipotent.”
Despite facing previous data breaches and legal actions, BreachForums resurfaced multiple times under new guises, prompting suspicions that it may now be a honeypot designed to ensnare cybercriminals for law enforcement purposes.
Recently, a website associated with the ShinyHunters extortion gang released an archive named breachedforum.7z, containing sensitive information.
Within this archive are three crucial files:
- shinyhunte.rs-the-story-of-james.txt
- databoose.sql
- breachedforum-pgp-key.txt.asc
A representative of the ShinyHunters extortion gang has distanced themselves from the distribution of this archive, as reported by BleepingComputer.
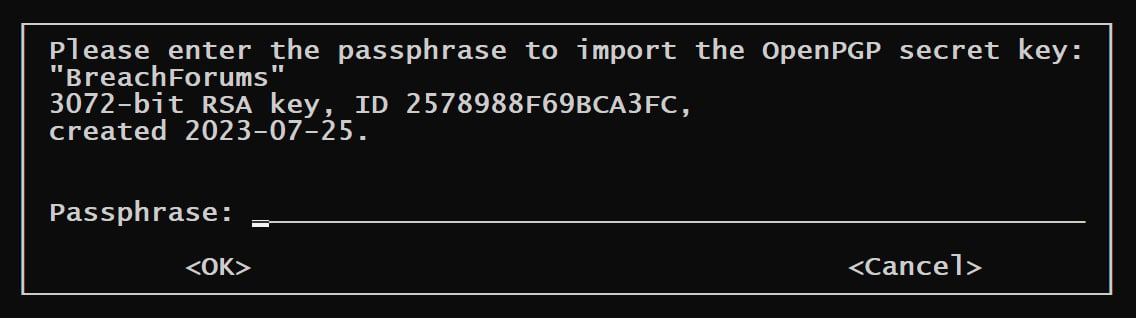
The ‘breachedforum-pgp-key.txt.asc’ file included in the archive is the PGP private key that BreachForums utilized to authenticate official messages from its administrators. Although the key has been exposed, it remains protected by a passphrase, preventing unauthorized usage for message signing.
Source: BleepingComputer
The “databoose.sql” file contains a MyBB users database table (mybb_users) with a total of 323,988 member records, including member display names, registration dates, and IP addresses.
Analysis conducted by BleepingComputer indicates that a majority of the IP addresses in the database correspond to local loopback IPs (0x7F000009/127.0.0.9), limiting their utility.
However, approximately 70,296 records feature public IP addresses, raising potential operational security (OPSEC) concerns for affected individuals and presenting value to law enforcement and cybersecurity researchers.
Notably, the most recent registration in the leaked database is dated August 11, 2025, coinciding with the closure of the previous BreachForums iteration at breachforums[.]hn following the apprehension of several alleged operators.
On that same day, a member of the ShinyHunters extortion gang asserted in the “Scattered Lapsus$ Hunters” Telegram channel that BreachForums operated as a law enforcement trap, a claim refuted by the forum’s administrators.
Subsequently, the breachforums[.]hn domain was confiscated by authorities in October 2025 after being repurposed for extorting companies impacted by the ShinyHunters’ Salesforce data theft operations.
Addressing the recent breach, the current BreachForums administrator, identified as “N/A,” disclosed that a backup of the MyBB user database table was temporarily exposed in an unsecured location and downloaded only once.
In a statement posted on BreachForums, “N/A” clarified, “This incident is not recent and stems from an old users-table leak dating back to August 2025 during the platform’s transition from the .hn domain.”
The administrator emphasized the transient nature of the exposure, highlighting that the folder containing the data was accessed only once during that timeframe.
While recommending members to utilize disposable email addresses for enhanced security and noting the prevalence of local IP addresses in the leaked data, the administrator acknowledged that the database still holds information potentially valuable to law enforcement authorities.
Update 1/10/26 04:02 PM ET: Following our initial report, cybersecurity firm Resecurity informed BleepingComputer that the BreachForums website now includes the password for accessing the PGP private key.
A separate security researcher corroborated the authenticity of the password for the key provided on the website.

As the adoption of MCP (Model Context Protocol) gains momentum for integrating LLMs with tools and data, cybersecurity teams are swiftly implementing best practices to safeguard these new services.
Download this free cheat sheet outlining 7 actionable best practices to enhance your security posture today.
-

 Facebook7 months ago
Facebook7 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook7 months ago
Facebook7 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook5 months ago
Facebook5 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook7 months ago
Facebook7 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook5 months ago
Facebook5 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook7 months ago
Facebook7 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook5 months ago
Facebook5 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple7 months ago
Apple7 months agoMeta discontinues Messenger apps for Windows and macOS
































