Security
Chinese State Hackers Unleash Advanced Malware on Telcos

An advanced persistent threat actor known as UAT-9244, linked to China, has been actively targeting telecommunication service providers in South America since 2024. Their attacks have focused on compromising Windows, Linux, and network-edge devices.
Researchers from Cisco Talos have identified this threat actor as closely associated with hacker groups FamousSparrow and Tropic Trooper, although UAT-9244 is considered a separate entity based on its unique tooling, tactics, techniques, and procedures (TTPs).
Based on their analysis, the researchers have a high level of confidence in their assessment, citing similarities in attack patterns and victim profiles across the various threat actors. While UAT-9244 shares similarities with Salt Typhoon in terms of target profile, a direct connection between the two clusters could not be conclusively established.
New Malware Campaign Targeting Telco Networks
The recent campaign orchestrated by UAT-9244 has introduced three new malware families: TernDoor, a Windows backdoor; PeerTime, a Linux backdoor utilizing BitTorrent; and BruteEntry, a brute-force scanner creating proxy infrastructure (ORBs).
TernDoor is distributed through DLL side-loading, leveraging the legitimate executable wsprint.exe to load malicious code from BugSplatRc64.dll. This code decrypts and executes the final payload in memory, injected into msiexec.exe.
This malware includes an embedded Windows driver, WSPrint.sys, enabling it to terminate, suspend, and resume processes on the infected system.
The malware achieves persistence through scheduled tasks and modifications to the Windows Registry, concealing the scheduled task in the process.
Furthermore, TernDoor can execute commands remotely, launch arbitrary processes, manipulate files, gather system information, and self-uninstall if necessary.
PeerTime, an ELF Linux backdoor, is designed to target multiple architectures (ARM, AARCH, PPC, MIPS), indicating its versatility in compromising a wide range of embedded systems and network devices commonly found in telco environments.

Source: Cisco Talos
Cisco Talos researchers have identified two versions of PeerTime, one written in C/C++ and the other based on Rust. Additionally, Simplified Chinese debug strings found in the instrumentor binary suggest the malware’s origin.
The payload of PeerTime is decrypted and loaded into memory, with the process being renamed to avoid detection.
Operating as an ELF-based peer-to-peer (P2P) backdoor, PeerTime utilizes the BitTorrent protocol for command-and-control (C2) communications, downloads and executes payloads from peers, and employs BusyBox to write files on the host system.
BruteEntry, the third component of the campaign, consists of a Go-based instrumentor binary and a brute-forcing module. Its primary function is to convert compromised devices into scanning nodes referred to as Operational Relay Boxes (ORBs).
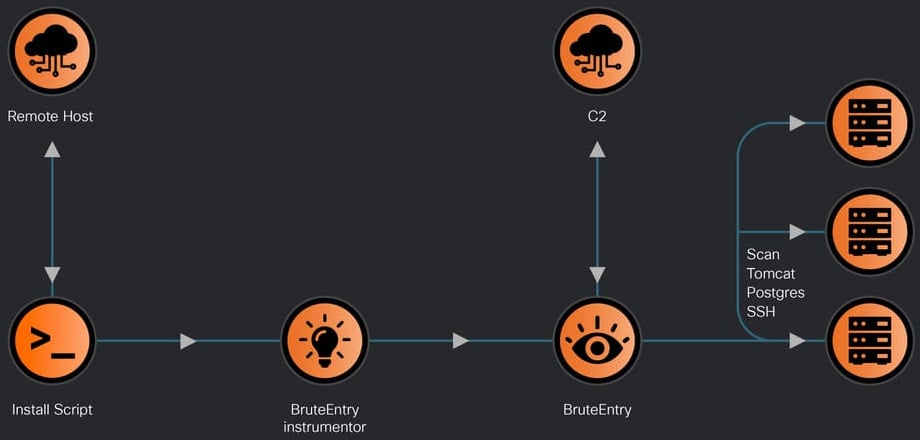
Source: Cisco Talos
The attacker leverages devices infected with BruteEntry to scan for new targets and attempt brute-force access to services such as SSH, Postgres, and Tomcat. The results of login attempts are relayed back to the C2 server along with task status updates.
In a technical report released by Cisco Talos, detailed insights into the functionalities of these malware components, their deployment methods, and persistence mechanisms are provided for cybersecurity professionals.
Cisco Talos researchers have compiled indicators of compromise (IoCs) associated with the observed activities of UAT-9244, enabling defenders to detect and thwart these attacks proactively.

Enhance your cybersecurity knowledge with the Red Report 2026, uncovering how new threats utilize advanced techniques to evade detection and operate stealthily within networks.
Access our analysis of 1.1 million malicious samples to identify the top 10 techniques and evaluate the efficacy of your security measures.
-

 Facebook8 months ago
Facebook8 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook8 months ago
Facebook8 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook6 months ago
Facebook6 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook8 months ago
Facebook8 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook6 months ago
Facebook6 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook8 months ago
Facebook8 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook6 months ago
Facebook6 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple8 months ago
Apple8 months agoMeta discontinues Messenger apps for Windows and macOS