Security
Director Patel’s Email Inbox Hacked by FBI, Investigation Underway
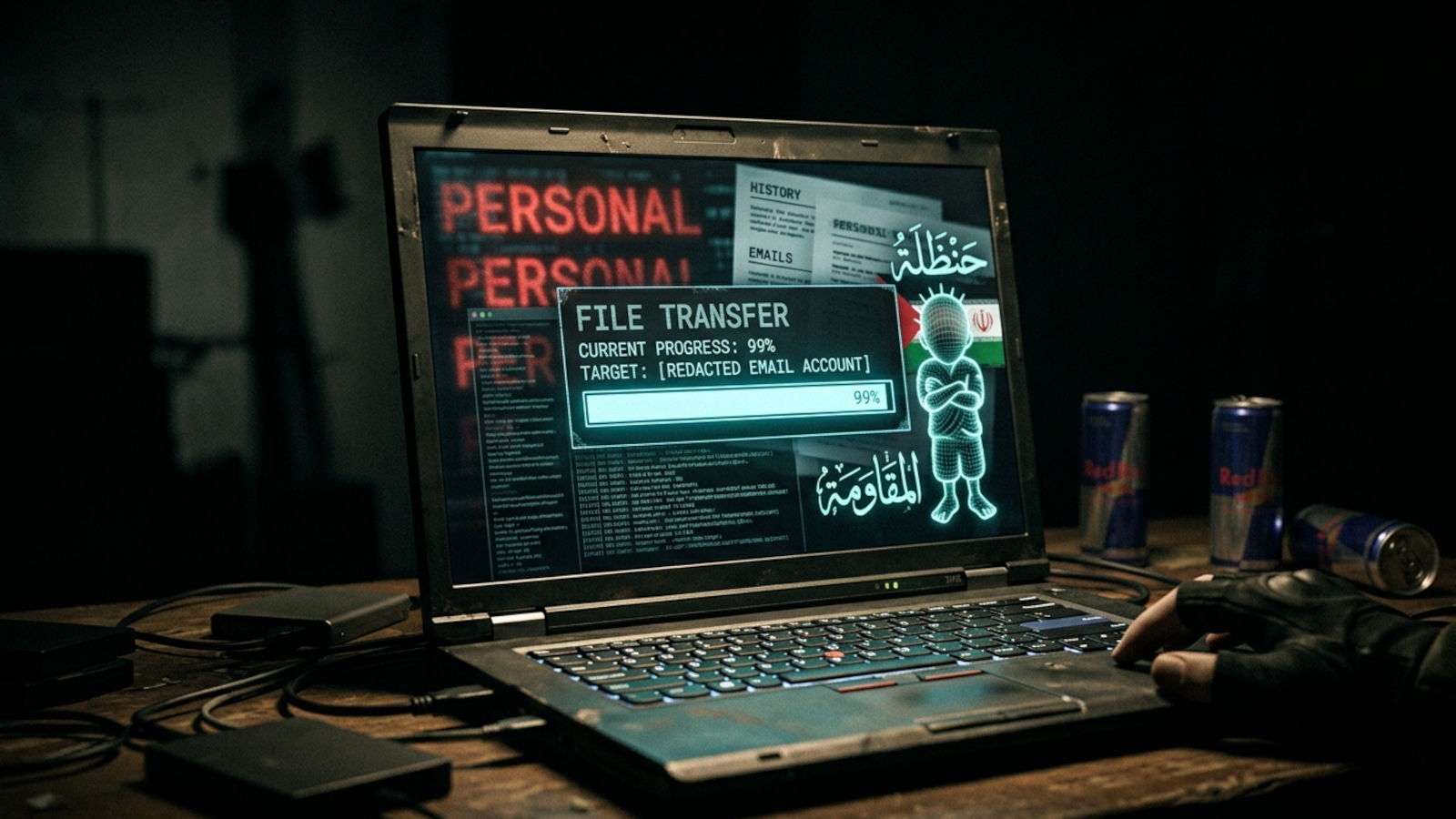
The Handala Hackers Breach FBI Director’s Personal Email Account
The Handala hackers, reportedly associated with Iran, have successfully breached the personal email account of FBI Director Kash Patel, leading to the exposure of photos and documents.
The FBI has acknowledged the breach, confirming that the stolen data was not recent and did not contain any government-related information.
On a recent announcement on one of their websites, the Handala threat actor claimed responsibility for infiltrating Patel’s personal Gmail inbox, emphasizing their ability to penetrate what was considered ‘impenetrable’ FBI systems within a few hours.
The motive behind the hack was allegedly in response to the FBI’s actions of seizing Handala domains and the U.S. government offering a reward of up to $10 million for information on the members of the threat group.
The hackers proceeded to make personal and confidential information of Kash Patel, including emails, conversations, documents, and classified files, available for public download after publishing proof of the breach.
source: BleepingComputer
Following the announcement, the threat actor released a series of watermarked personal photos and documents extracted from Patel’s inbox, in addition to email correspondence predating his tenure as FBI director.
The FBI, in a statement to BleepingComputer, acknowledged the targeting of Director Patel’s personal email information by malicious actors and assured that necessary precautions had been taken to minimize potential risks.
“The FBI is aware of malicious actors targeting Director Patel’s personal email information, and we have taken all necessary steps to mitigate potential risks associated with this activity. The information in question is historical in nature and involves no government information,” – the Federal Bureau of Investigation
The Handala hacktivist group, also known as Handala Hack, Hatef, and Hamsa, gained notoriety after breaching the Microsoft environment of medical technology giant Stryker and wiping nearly 80,000 devices.
Operating as a hacktivist persona for Iran’s Ministry of Intelligence and Security (MOIS), the Handala group emerged in December 2023 and has been actively involved in cyber activities.
In light of the breach of Director Patel’s personal email account, the FBI reiterated the $10 million reward offered by the Department of State’s Rewards for Justice for information leading to the identification of the Handala Hack Team based in Iran.
Automated Pentesting and Cybersecurity

Automated pentesting proves the path exists. BAS proves whether your controls stop it. Most teams run one without the other.
This whitepaper maps six validation surfaces, shows where coverage ends, and provides practitioners with three diagnostic questions for any tool evaluation.
Automated pentesting is crucial in identifying vulnerabilities in your systems, while BAS (Behavioral Analytics System) helps assess the effectiveness of your security controls. It’s essential to utilize both tools to ensure comprehensive cybersecurity.
This whitepaper delves into six validation surfaces, highlighting areas where coverage may be lacking and offering three diagnostic questions for evaluating cybersecurity tools effectively.
-

 Facebook7 months ago
Facebook7 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook7 months ago
Facebook7 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook5 months ago
Facebook5 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook7 months ago
Facebook7 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook5 months ago
Facebook5 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook7 months ago
Facebook7 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook5 months ago
Facebook5 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple7 months ago
Apple7 months agoMeta discontinues Messenger apps for Windows and macOS































