A New Malware Loader, DeepLoad, Discovered in ClickFix Social Engineering Campaign
A recently uncovered malware loader known as DeepLoad has been linked to a sophisticated social engineering campaign utilizing the ClickFix tactic for distribution.
According to researchers Thassanai McCabe and Andrew Currie from ReliaQuest, DeepLoad employs AI-assisted obfuscation techniques and process injection to avoid detection by security tools. The malware loader focuses on credential theft, capturing passwords and sessions even if the initial loader is blocked.
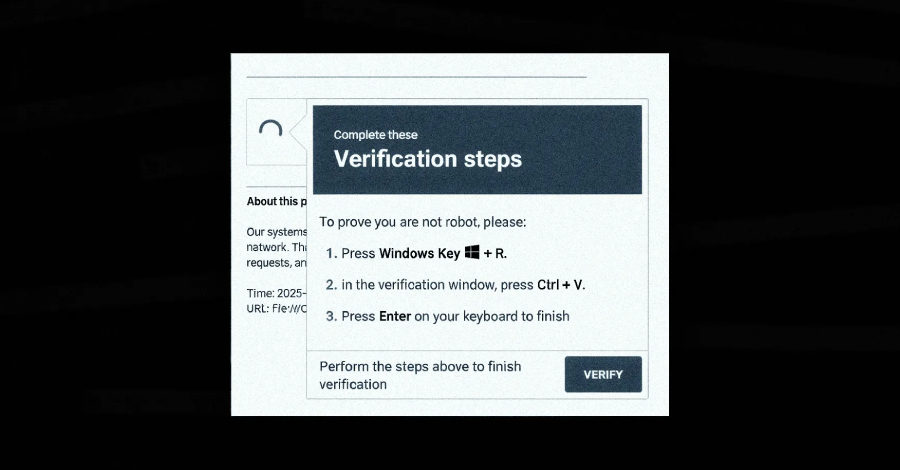
The attack begins with a ClickFix lure that tricks users into running PowerShell commands by pasting them into the Windows Run dialog under the guise of addressing a non-existent issue. This initiates the download and execution of an obfuscated PowerShell loader using the legitimate Windows utility “mshta.exe.”
DeepLoad conceals its true functionality by obfuscating code with meaningless variable assignments, likely utilizing an AI tool for the obfuscation layer. The malware blends in with normal Windows processes to evade detection, including hiding the payload within a legitimate Windows process named “LockAppHost.exe.”
To bypass monitoring hooks and evade detection, DeepLoad disables PowerShell command history, invokes native Windows core functions directly, and generates a secondary component on-the-fly using PowerShell’s Add-Type feature to compile and run code written in C#.
Another evasion tactic employed by DeepLoad is asynchronous procedure call (APC) injection, allowing the main payload to run inside a trusted Windows process without writing a decoded payload to disk. This method ensures persistence and avoids detection by security controls.
DeepLoad is designed to steal browser passwords and drops a malicious browser extension to intercept credentials entered on login pages. The malware can also automatically detect and infect removable media devices, spreading the infection to other machines.
Additionally, DeepLoad leverages Windows Management Instrumentation (WMI) to reinfect a clean host without user interaction, breaking detection rules and quietly re-executing the attack at a later time.
Discovery of Kiss Loader and Its Distribution Method
In a separate discovery, G DATA revealed the existence of Kiss Loader, a malware loader distributed through Windows Internet Shortcut files attached to phishing emails. The loader connects to a remote WebDAV resource and executes a series of scripts to download and run the Python-based Kiss Loader, which then deploys the Venom RAT variant using APC injection.
The threat actor behind Kiss Loader claims to be from Malawi, but the extent of the malware’s distribution and any potential malware-as-a-service (MaaS) offerings remain unknown.
Both DeepLoad and Kiss Loader highlight the evolving landscape of cyber threats, emphasizing the importance of robust cybersecurity measures to defend against sophisticated malware attacks.