Security
Combatting Helpdesk Impersonation Attacks: Safeguarding Teams from Abuse

Microsoft has issued a warning regarding the increasing abuse of external Microsoft Teams collaboration by threat actors, who are utilizing legitimate tools for unauthorized access and lateral movement within enterprise networks.
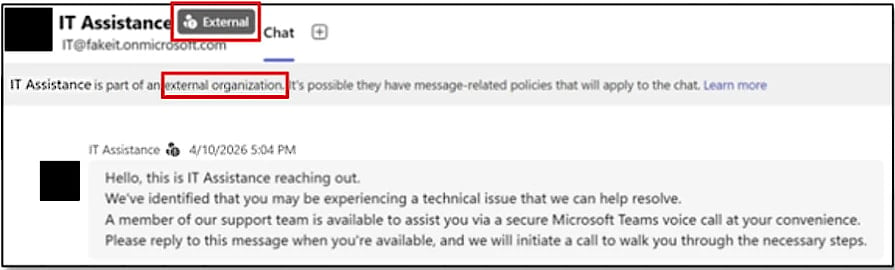
In these attacks, hackers pretend to be IT or helpdesk personnel, reaching out to employees through cross-tenant chats and persuading them to provide remote access for the purpose of stealing data.
Multiple intrusions have been observed by Microsoft following a similar attack pattern, involving the use of commercial remote management software like Quick Assist and the Rclone utility to transfer files to an external cloud storage service.

According to Microsoft, distinguishing malicious activity from normal operations has become challenging due to the extensive use of legitimate applications and native administrative protocols.
Microsoft stated, “Threat actors are increasingly exploiting external Microsoft Teams collaboration to impersonate IT or helpdesk personnel and coerce users into granting remote assistance access.”
The company added, “Attackers can utilize trusted tools and native administrative protocols to navigate through the enterprise and prepare sensitive data for exfiltration, often blending in with routine IT support activities during the intrusion process.”
Complex Attack Process
In a recent report, Microsoft outlined a nine-stage attack process that begins with threat actors contacting targets through external Teams chat, posing as IT staff members from the company and claiming the need to address account issues or perform security updates.
The objective is to convince the target to initiate a remote support session, typically through Quick Assist, granting the attacker direct control over the employee’s device.
Source: Microsoft
Following this, the attacker conducts rapid reconnaissance using Command Prompt and PowerShell to assess privileges, domain membership, and network reachability for potential lateral movement.
Subsequently, the attacker places a small payload bundle in user-writable locations such as ProgramData and executes malicious code through a trusted, signed application (e.g., Autodesk, Adobe Acrobat/Reader, Windows Error Reporting, data loss prevention software) via DLL side-loading.
The communication to the established command-and-control (C2) through HTTPS blends in with normal outbound traffic, making detection more challenging.
With the infection established and persistence ensured through Windows Registry modifications, the attacker proceeds to exploit Windows Remote Management (WinRM) to move laterally across the network, targeting domain-joined systems and high-value assets like domain controllers.
Additional remote management software tools are deployed on accessible systems, and tools like Rclone are used to gather and transfer sensitive data to external cloud storage locations.
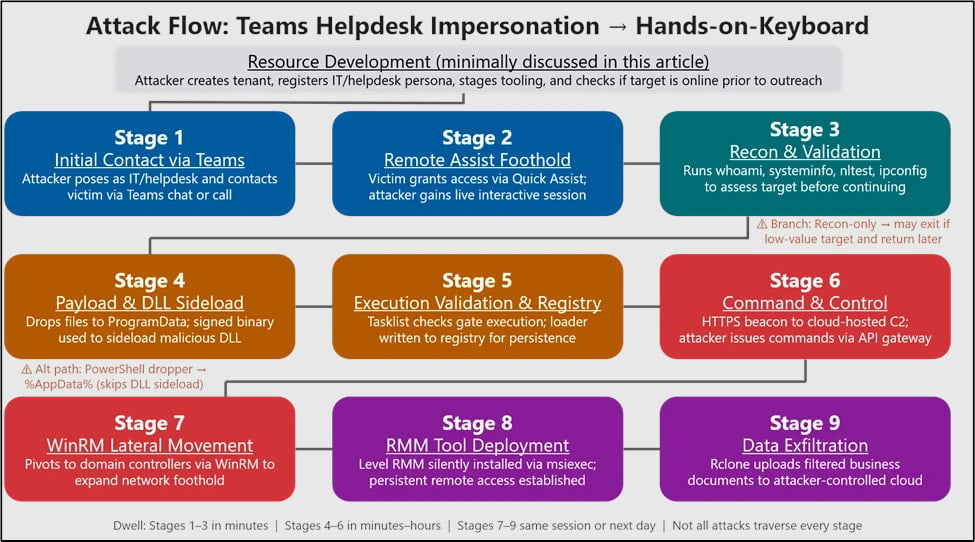
Source: Microsoft
Microsoft highlights that the exfiltration phase is highly targeted, employing filters to focus on valuable information, reduce transfer volume, and enhance operational stealth.
Users are advised by Microsoft to approach external Teams contacts with caution by default and to consider restricting or closely monitoring remote assistance tools, as well as limiting WinRM usage to controlled systems.
Furthermore, Microsoft emphasizes the importance of Teams security warnings that flag communications from external sources and potential phishing attempts.

An AI exploit combined four zero-days to bypass renderer and OS sandboxes, signaling a wave of new exploits. Learn about autonomous validation at the Autonomous Validation Summit (May 12 & 14) to identify vulnerabilities, validate controls, and close the remediation loop.
-

 Facebook8 months ago
Facebook8 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook8 months ago
Facebook8 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook6 months ago
Facebook6 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook8 months ago
Facebook8 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook6 months ago
Facebook6 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook8 months ago
Facebook8 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook6 months ago
Facebook6 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple8 months ago
Apple8 months agoMeta discontinues Messenger apps for Windows and macOS
































