Security
Beware of the Latest Wave of OAuth Phishing Attacks Targeting Microsoft 365 Accounts

There is a growing trend of multiple threat actors targeting Microsoft 365 accounts through phishing attacks that exploit the OAuth device code authorization mechanism.
In these attacks, hackers deceive victims into entering a device code on Microsoft’s legitimate device login page. This action unknowingly grants access to an attacker-controlled application, allowing them to infiltrate the target account without needing to steal credentials or bypass multi-factor authentication (MFA).
Although this method is not new, email security company Proofpoint has noted a significant increase in the volume of these attacks since September. The attacks are carried out by both financially motivated cybercriminals like TA2723 and state-aligned threat actors.

“Proofpoint Threat Research has observed multiple threat clusters using device code phishing to trick users into granting a threat actor access to their Microsoft 365 account,” the security company warned, highlighting that widespread campaigns utilizing these attack flows are considered “highly unusual.”
Tools and campaigns
Proofpoint has identified various attack chains in these campaigns, with slight variations. However, they all involve tricking victims into entering a device code on Microsoft’s legitimate device login portals.
In some instances, the device code is presented as a one-time password, while in others, the lure may be a token re-authorization notification.
The researchers have observed two phishing kits used in these attacks: SquarePhish v1 and v2, and Graphish, which streamline the phishing process.
SquarePhish is a publicly available tool used for red teaming, targeting OAuth device grant authorization flows through QR codes, mimicking legitimate Microsoft MFA/TOTP setups.
Graphish, on the other hand, is a malicious phishing kit shared on underground forums that supports OAuth abuse, Azure App Registrations, and adversary-in-the-middle (AiTM) attacks.
Regarding the campaigns observed by Proofpoint, three have been highlighted in the report:
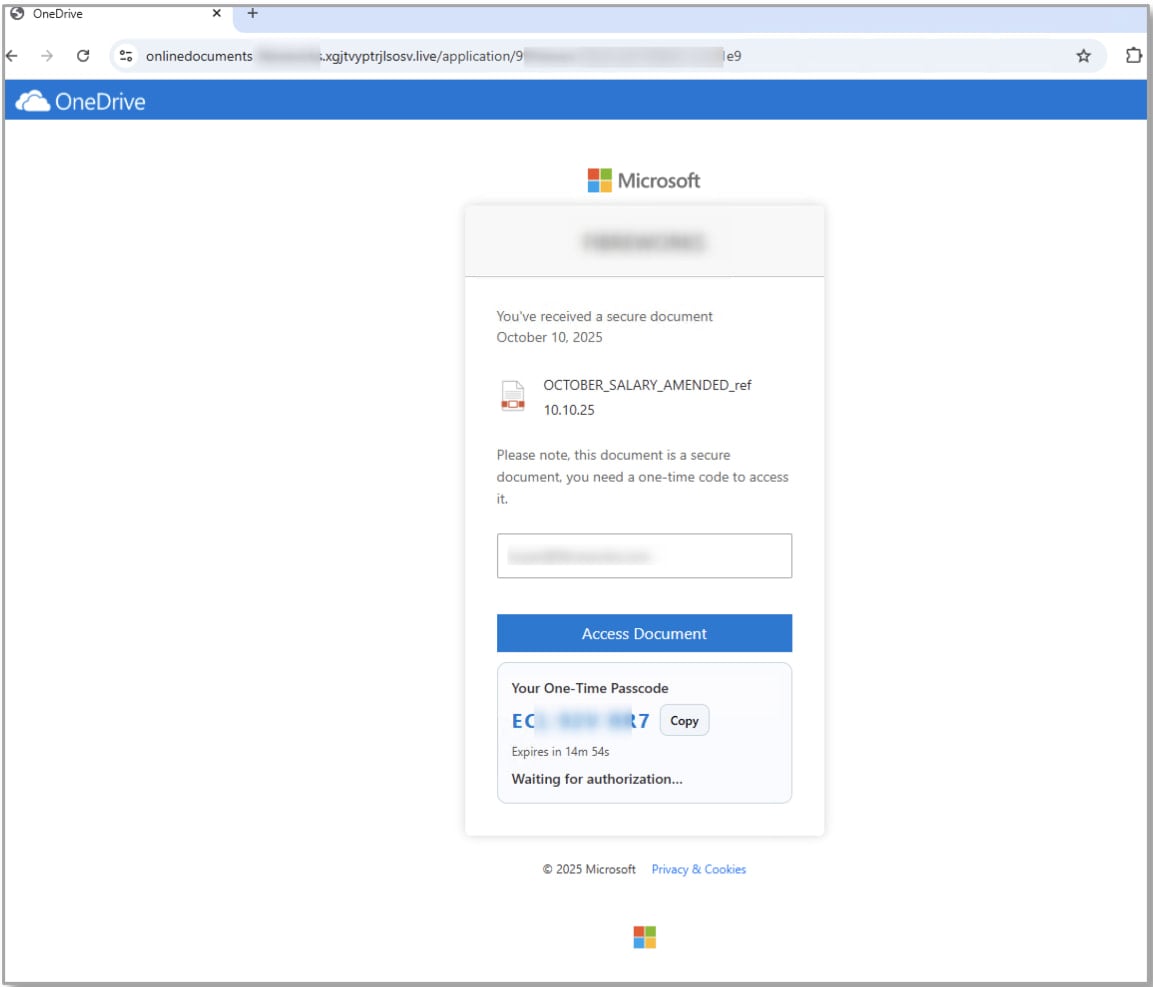
- Salary bonus attacks – This campaign uses document-sharing lures and localized company branding to entice recipients to click on links leading to attacker-controlled websites. Victims are then prompted to complete “secure authentication” by entering a provided code on Microsoft’s legitimate device login page, unknowingly authorizing an attacker-controlled application.
.jpg)
Source: Proofpoint
- TA2723 attacks – This actor, known for high-volume credential-phishing and previously spoofing Microsoft OneDrive, LinkedIn, and DocuSign, began using OAuth device code phishing in October. Early phases of these campaigns likely utilized SquarePhish2, with later waves potentially transitioning to the Graphish phishing kit.
Source: Proofpoint
- State-aligned activity – Since September 2025, Proofpoint has observed a suspected Russia-aligned threat actor, identified as UNK_AcademicFlare, abusing OAuth device code authorization for account takeover. This actor uses compromised government and military email accounts to establish trust before sharing links that mimic OneDrive, leading victims into a device code phishing scenario. The targets primarily include government, academic, think tank, and transportation sectors in the U.S. and Europe.
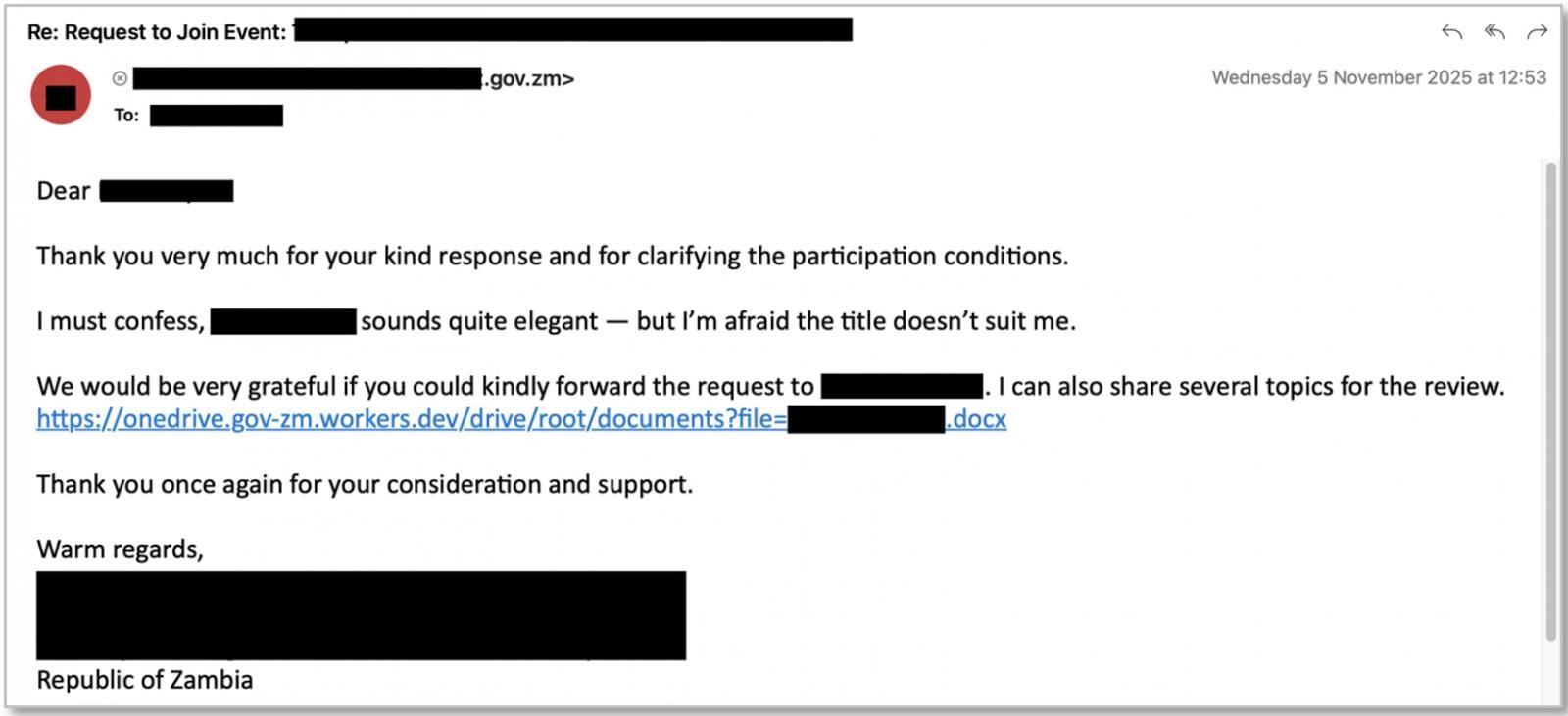
Source: Proofpoint
To prevent these attacks, organizations are advised to implement Microsoft Entra Conditional Access where possible and consider implementing a policy on sign-in origin.

Challenges with Identity and Access Management (IAM) extend beyond IT and impact the entire business.
This comprehensive guide explores the limitations of traditional IAM practices, showcases effective IAM strategies, and provides a simple checklist for developing a scalable IAM approach.
-

 Facebook7 months ago
Facebook7 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook7 months ago
Facebook7 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook5 months ago
Facebook5 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook7 months ago
Facebook7 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook5 months ago
Facebook5 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook7 months ago
Facebook7 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook5 months ago
Facebook5 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple7 months ago
Apple7 months agoMeta discontinues Messenger apps for Windows and macOS