Security
Critical Security Alert: Massive Exposure of Fortinet Firewalls Leads to Widespread 2FA Bypass Attacks

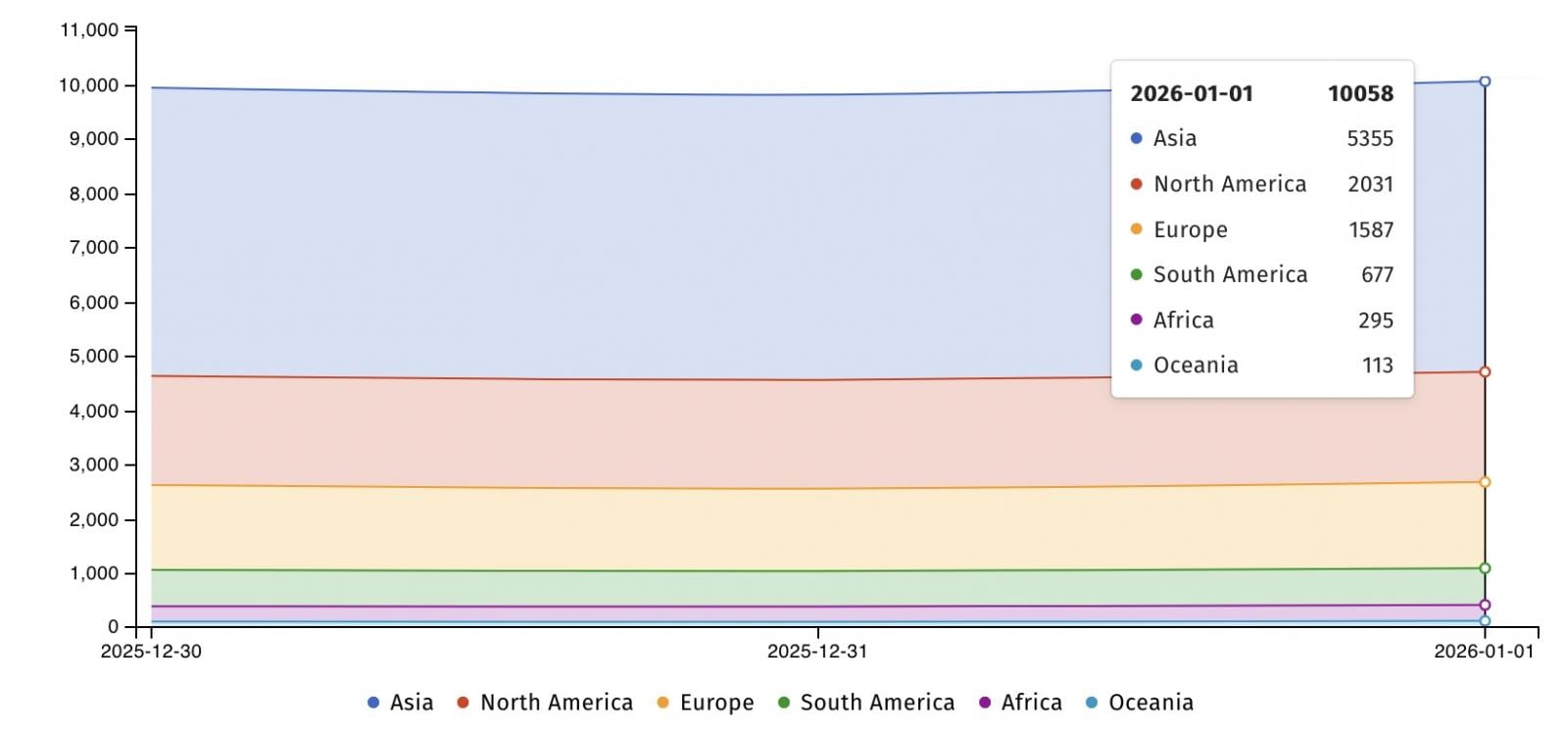
Over 10,000 Fortinet Firewalls Still Vulnerable to Critical 2FA Bypass Vulnerability
Fortinet firewalls are at risk as over 10,000 devices remain exposed and vulnerable to attacks exploiting a critical two-factor authentication (2FA) bypass vulnerability that has been known for five years.
In July 2020, Fortinet released updates for FortiOS versions 6.4.1, 6.2.4, and 6.0.10 to address this flaw, identified as CVE-2020-12812. Admins who couldn’t immediately apply the patches were advised to disable username-case-sensitivity to prevent 2FA bypass attempts on their devices.
The severity of this security flaw, rated at 9.8/10, lies in the improper authentication of FortiGate SSL VPN, allowing unauthorized access to unpatched firewalls without the required second factor of authentication (FortiToken) when the username’s case is modified.

Recent reports indicate that attackers are still leveraging CVE-2020-12812 to target vulnerable Fortinet firewalls, especially those configurations that require LDAP to be enabled.
Fortinet highlighted the ongoing abuse of the July 2020 vulnerability, emphasizing specific configurations that are being exploited in the wild.
Internet security watchdog Shadowserver revealed that more than 10,000 Fortinet firewalls are still exposed online and unpatched against CVE-2020-12812, making them susceptible to these ongoing attacks, with a significant number of vulnerable devices located in the United States.
In April 2021, CISA and the FBI cautioned about state-sponsored hacking groups targeting Fortinet FortiOS instances using exploits for multiple vulnerabilities, including CVE-2020-12812, to bypass 2FA.
Subsequently, CISA listed CVE-2020-12812 as a known exploited vulnerability, linking it to ransomware attacks and instructing U.S. federal agencies to secure their systems by May 2022.
Fortinet vulnerabilities, particularly zero-day exploits, are frequently targeted by threat actors. For example, cybersecurity firm Arctic Wolf raised an alarm in December about threat actors exploiting a critical authentication bypass vulnerability (CVE-2025-59718) to compromise admin accounts via malicious single sign-on (SSO) logins.
Fortinet also disclosed the exploitation of FortiWeb zero-day vulnerabilities, with one (CVE-2025-58034) being actively abused and another (CVE-2025-64446) silently patched after widespread attacks.
Moreover, the Chinese Volt Typhoon threat group exploited two FortiOS flaws (CVE-2023-27997 and CVE-2022-42475) to compromise a Dutch Ministry of Defence military network using custom Coathanger remote access trojan malware in February 2025.

As Model Context Protocol (MCP) gains prominence in connecting LLMs to tools and data, security teams are actively enhancing the safety of these new services.
Discover 7 best practices in this free cheat sheet to enhance your security measures.
-

 Facebook7 months ago
Facebook7 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook7 months ago
Facebook7 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook5 months ago
Facebook5 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook7 months ago
Facebook7 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook5 months ago
Facebook5 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook7 months ago
Facebook7 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook5 months ago
Facebook5 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple7 months ago
Apple7 months agoMeta discontinues Messenger apps for Windows and macOS






























