Security
DanaBot Resurfaces: Windows Users at Risk as Malware Returns After 6-Month Hiatus
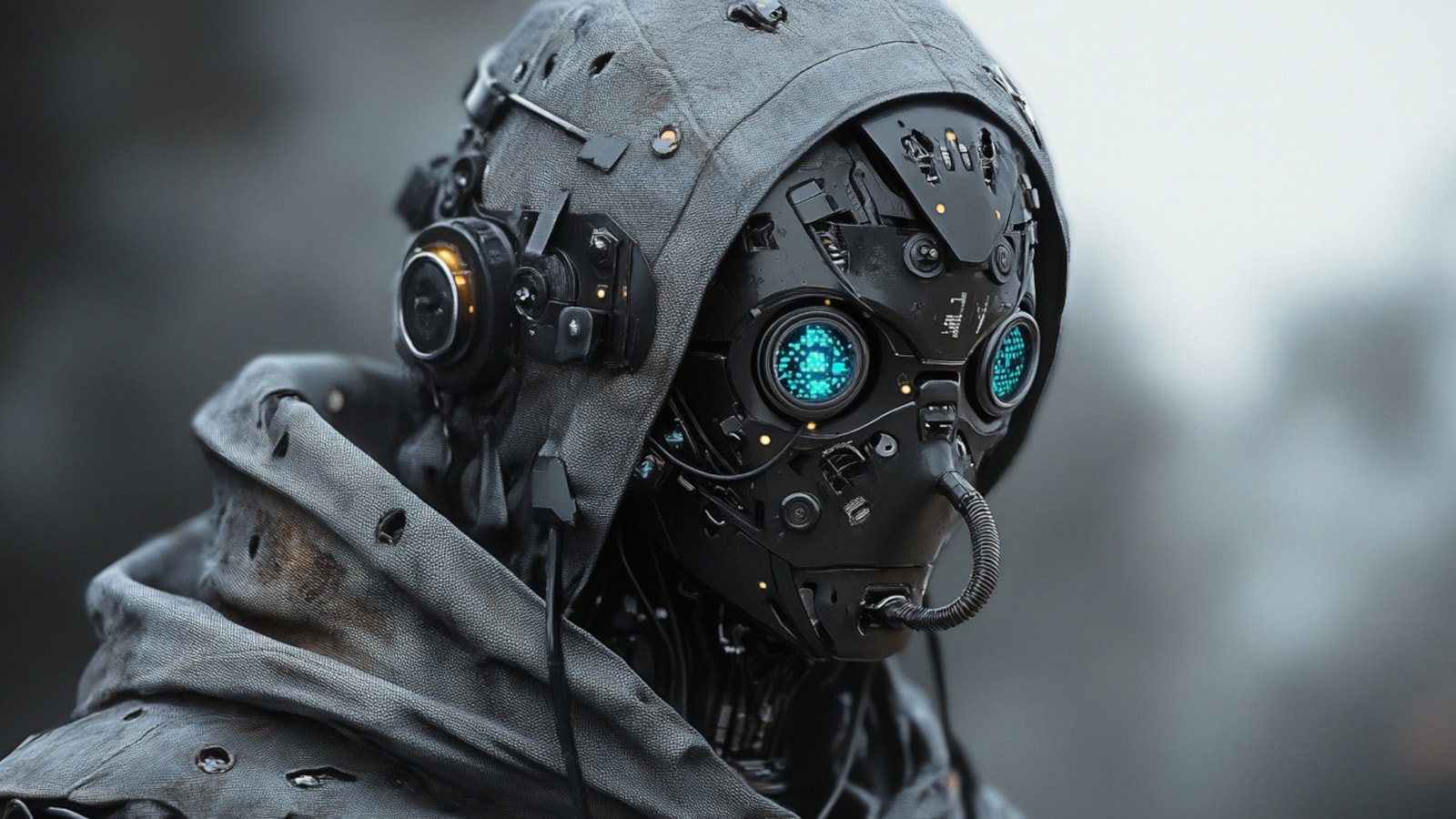
The Return of DanaBot Malware: New Variant Emerges After 6-Month Hiatus
After a significant disruption in May due to law enforcement’s Operation Endgame, the notorious DanaBot malware has resurfaced with a new version, observed in recent attacks.
Security researchers at Zscaler ThreatLabz have identified a fresh variant of DanaBot, known as version 669, featuring a command-and-control (C2) infrastructure utilizing Tor domains (.onion) and “backconnect” nodes.
Zscaler has also uncovered several cryptocurrency addresses used by threat actors to receive stolen funds, including BTC, ETH, LTC, and TRX.

The origins of DanaBot trace back to its disclosure by Proofpoint researchers as a Delphi-based banking trojan distributed via email and malvertising.
Operating under a malware-as-a-service (MaaS) model, DanaBot was available for rent to cybercriminals for a subscription fee.
Over time, the malware transformed into a modular information stealer and loader, primarily targeting credentials and cryptocurrency wallet data stored in web browsers.
Despite facing disruptions, DanaBot persisted in various campaigns, resurfacing intermittently since 2021 and posing a persistent threat to online users.
In a significant development in May, international law enforcement launched ‘Operation Endgame,’ dismantling DanaBot’s infrastructure and leading to arrests and asset seizures that severely impacted its operations.
However, according to Zscaler, DanaBot has resurfaced with a reconstructed infrastructure, highlighting the resilience of cybercriminals in pursuing financial gains, even following extended disruptions.
The resurgence of DanaBot underscores the adaptability of cybercriminals, especially in the absence of key arrests, as they continue to exploit vulnerabilities for malicious purposes.
Common methods of initial access observed in DanaBot infections include malicious emails (via links or attachments), SEO poisoning, and malvertising campaigns, some of which have escalated to ransomware attacks.
To bolster defenses against DanaBot attacks, organizations are advised to update their security tools and incorporate the latest indicators of compromise (IoCs) identified by Zscaler into their blocklists.

Empower your team with expert guidance on secrets management and secure coding practices. Download our comprehensive cheat sheet to streamline your security protocols.
-

 Facebook6 months ago
Facebook6 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook6 months ago
Facebook6 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook4 months ago
Facebook4 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook6 months ago
Facebook6 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook4 months ago
Facebook4 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook6 months ago
Facebook6 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook4 months ago
Facebook4 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple6 months ago
Apple6 months agoMeta discontinues Messenger apps for Windows and macOS