Security
Corporate Cyber Invasion: New Windows Malware Threatens Fortune 100 Firm

Ransomware Attackers Target Fortune 100 Finance Company with New Malware Strain
A recent cyber attack on a Fortune 100 finance company involved the use of a new malware strain called PDFSider. This malicious software was utilized by the attackers to deliver harmful payloads on Windows systems.
The attackers employed social engineering tactics to gain remote access by posing as technical support workers. They attempted to deceive company employees into installing Microsoft’s Quick Assist tool, allowing them to infiltrate the network.
PDFSider was discovered by researchers at cybersecurity firm Resecurity during an incident response. They describe the malware as a stealthy backdoor that provides long-term access to compromised systems, exhibiting characteristics commonly associated with Advanced Persistent Threat (APT) tradecraft.
Legitimate EXE, Malicious DLL
According to a spokesperson from Resecurity, PDFSider has been observed in Qilin ransomware attacks. The threat hunting team at Resecurity has noted that multiple ransomware actors are actively using the backdoor to deploy their malicious payloads.
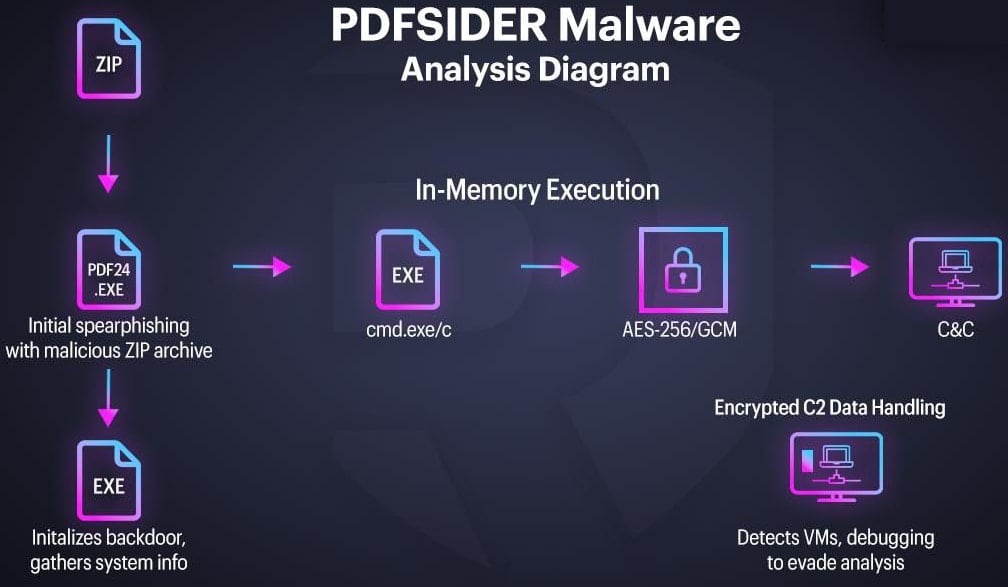
The PDFSider backdoor is distributed through spearphishing emails containing a ZIP archive. This archive includes a legitimate, digitally signed executable for the PDF24 Creator tool, alongside a malicious version of a DLL called cryptbase.dll. When the legitimate executable is run, it loads the attacker’s DLL file, enabling code execution on the system through a technique known as DLL side-loading.
Attackers have also attempted to trick email recipients into launching the malicious file by using decoy documents tailored to the targets. In one instance, they impersonated a Chinese government entity as the document’s author.
Resecurity explains that while the EXE file has a valid signature, vulnerabilities in the PDF24 software allowed attackers to exploit it to load the malware, bypassing Endpoint Detection and Response (EDR) systems effectively.
With the rise of AI-powered coding, cybercriminals are finding vulnerable software more easily. PDFSider loads directly into memory to minimize disk artifacts and utilizes anonymous pipes to execute commands via CMD.
Infected hosts receive a unique identifier, and their system information is gathered and sent to the attacker’s Virtual Private Server (VPS) over DNS (port 53). The malware uses the Botan 3.0.0 cryptographic library and AES-256-GCM for encryption during command-and-control (C2) exchanges.
PDFSider employs anti-analysis mechanisms such as RAM size checks and debugger detection to avoid detection in sandboxes. Resecurity suggests that the malware is more aligned with espionage tradecraft than financially motivated attacks, designed to maintain covert access, execute remote commands, and communicate securely.
Source: Resecurity

As budget season approaches, over 300 CISOs and security leaders have shared their insights on planning, spending, and prioritizing for the year ahead. Discover emerging trends and benchmark strategies with this comprehensive report.
Learn how top leaders are translating investments into tangible results and addressing cybersecurity challenges in 2026.
-

 Facebook7 months ago
Facebook7 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook7 months ago
Facebook7 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook5 months ago
Facebook5 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook7 months ago
Facebook7 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook6 months ago
Facebook6 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook7 months ago
Facebook7 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook6 months ago
Facebook6 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple7 months ago
Apple7 months agoMeta discontinues Messenger apps for Windows and macOS































