Security
CISA Sounds Alarm on Active Exploitation of Apache ActiveMQ Vulnerability
Apache ActiveMQ Vulnerability Actively Exploited, CISA Warns
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) issued a warning regarding a high-severity Apache ActiveMQ vulnerability that is currently being exploited in attacks. This vulnerability, tracked as CVE-2026-34197, has been present for 13 years and was recently discovered by Horizon3 researcher Naveen Sunkavally using the Claude AI assistant.
Apache ActiveMQ is widely known as the leading open-source Java-based message broker used for asynchronous communication between applications. This security flaw, which went undetected for over a decade, allows authenticated threat actors to execute arbitrary code through injection attacks due to improper input validation.
Sunkavally emphasized the critical nature of this vulnerability and highlighted the importance of organizations running ActiveMQ to prioritize patching. The Apache maintainers have released patches for ActiveMQ Classic versions 6.2.3 and 5.19.4 on March 30 to address this issue.
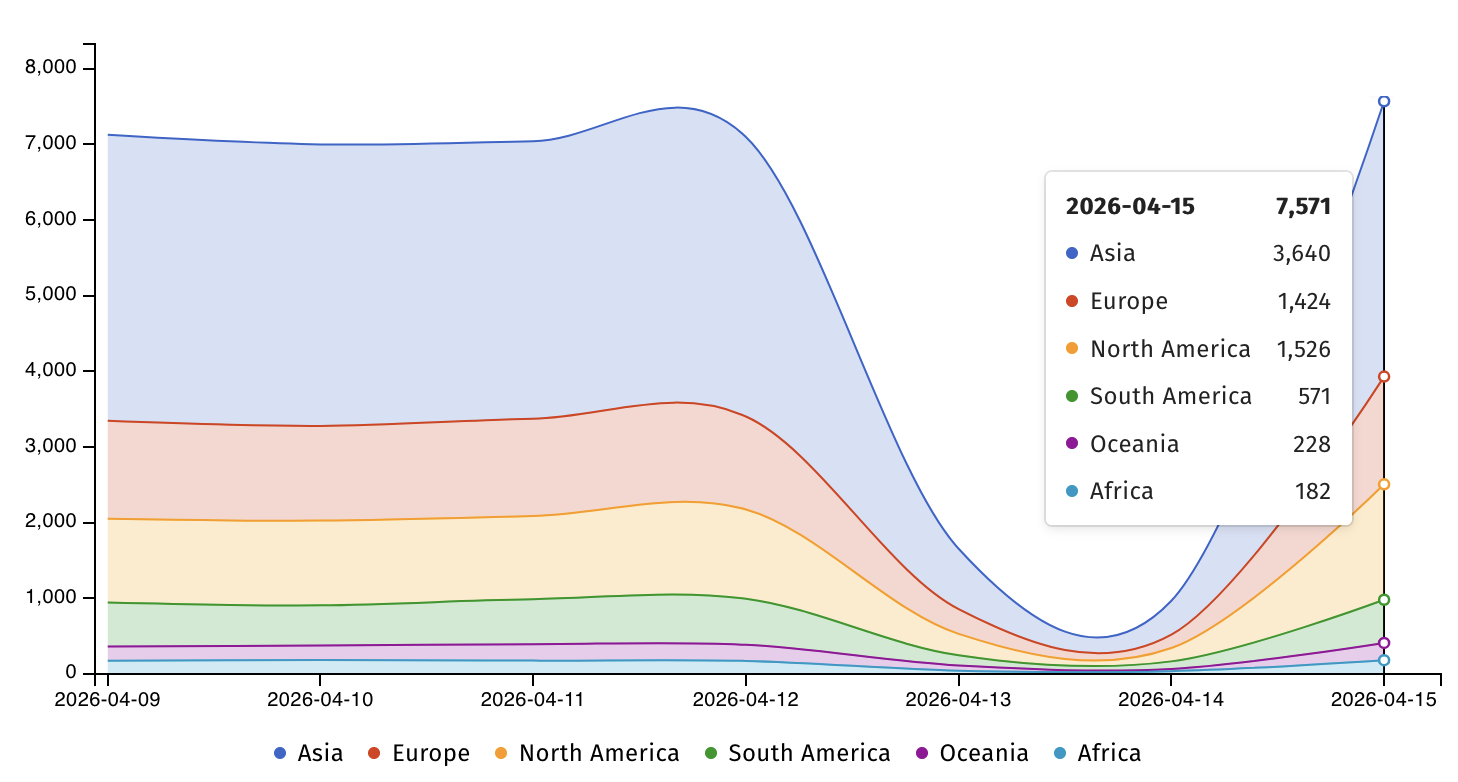
Horizon3 warned organizations about the repeated targeting of ActiveMQ by real-world attackers and the well-known methods for exploiting and post-exploitation of this platform. ShadowServer, the threat monitoring service, currently identifies over 7,500 Apache ActiveMQ servers exposed online.
CISA Mandate and Recommendations
CISA has added CVE-2026-34197 to its Known Exploited Vulnerabilities (KEV) Catalog and directed Federal Civilian Executive Branch (FCEB) agencies to patch ActiveMQ servers by April 30, following Binding Operational Directive (BOD) 22-01 guidelines. Horizon3 researchers suggested monitoring ActiveMQ broker logs for signs of exploitation and emphasized the significant risks posed by such vulnerabilities to the federal enterprise.
CISA urged private-sector entities to prioritize patching for CVE-2026-35616 and secure their networks promptly, even though BOD 22-01 specifically applies to U.S. federal agencies. The cybersecurity agency also cautioned against the exploitation of two other Apache ActiveMQ vulnerabilities, CVE-2023-46604 and CVE-2016-3088, with the former targeted by the TellYouThePass ransomware gang as a zero-day flaw.

AI chained four zero-days into one exploit that bypassed both renderer and OS sandboxes. A wave of new exploits is coming.
At the Autonomous Validation Summit (May 12 & 14), witness how autonomous, context-rich validation identifies vulnerabilities, proves controls, and facilitates remediation.
-

 Facebook7 months ago
Facebook7 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook8 months ago
Facebook8 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook6 months ago
Facebook6 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook8 months ago
Facebook8 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook6 months ago
Facebook6 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook8 months ago
Facebook8 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook6 months ago
Facebook6 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple7 months ago
Apple7 months agoMeta discontinues Messenger apps for Windows and macOS































