Security
Microsoft Bolsters Windows Security with Enhanced Remote Desktop File Protections
Microsoft has recently implemented enhanced protections for Windows to safeguard against phishing attacks exploiting Remote Desktop connection (.rdp) files. These new measures include warnings and the default disabling of risky shared resources.
Remote Desktop Protocol (RDP) files are commonly utilized in enterprise settings to establish connections with remote systems. System administrators often preconfigure these files to automatically redirect local resources to the remote host.
Unfortunately, threat actors have been leveraging this functionality in phishing campaigns. For instance, the Russian state-sponsored APT29 hacking group has previously utilized rogue RDP files to illicitly steal data and credentials from unsuspecting victims.

Upon opening these compromised files, connections can be established with attacker-controlled systems, allowing for the redirection of local drives to the connected device. This enables the attacker to pilfer files and credentials stored on the disk.
Moreover, these malicious files can intercept clipboard data, including sensitive information like passwords, or reroute authentication mechanisms such as smart cards or Windows Hello to impersonate users.
New Protections for RDP Implementation
As part of the April 2026 cumulative updates for Windows 10 (KB5082200) and Windows 11 (KB5083769 and KB5082052), Microsoft has rolled out new protections to thwart the misuse of malicious RDP connection files on devices.
Microsoft issued a warning stating, “Malicious actors exploit this capability by distributing RDP files via phishing emails.” Once a victim opens such a file, their device silently connects to a server controlled by the attacker, facilitating access to files, credentials, and more.
Following the installation of this update, when users attempt to open an RDP file for the first time, an educational prompt will be displayed. This prompt explains the nature of RDP files and highlights associated risks. Users are required to acknowledge these risks and press OK to prevent further alerts.
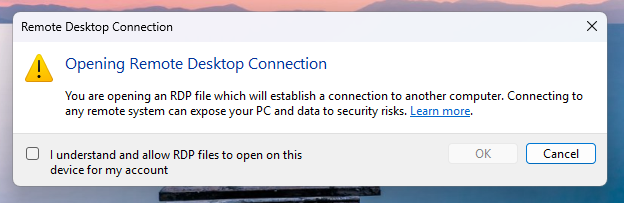
Source: Microsoft
Subsequent attempts to open RDP files will trigger a security dialog before any connection is established. This dialog provides information on whether the RDP file is signed by a verified publisher, the remote system’s address, and details all local resource redirections, with all options initially disabled.
If an RDP file lacks digital signature, Windows displays a “Caution: Unknown remote connection” warning, identifying the publisher as unknown, signifying the inability to verify the file’s creator.
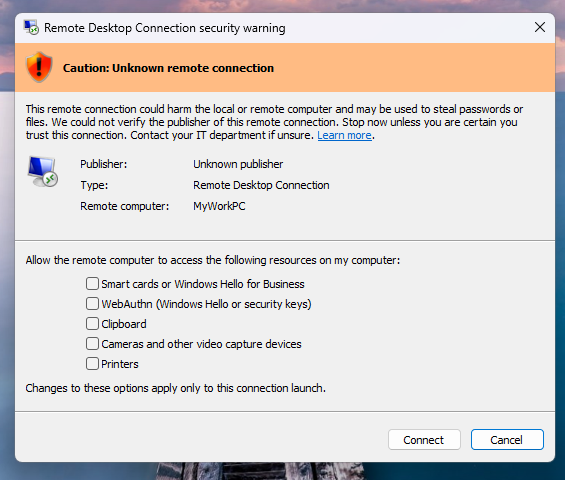
Source: Microsoft
For digitally signed RDP files, Windows will display the publisher’s information, still advising users to validate their legitimacy prior to connection.
It is important to note that these enhanced protections pertain solely to connections initiated through opening RDP files and not those established via the Windows Remote Desktop client.
Microsoft offers the option for Administrators to temporarily disable these protections by adjusting the RedirectionWarningDialogVersion value in the HKLM\Software\Policies\Microsoft\Windows NT\Terminal Services\Client Registry key to 1. However, given the historical misuse of RDP files in cyberattacks, it is strongly recommended to maintain these protections enabled.

Automated penetration testing validates the existing vulnerabilities, while Breach and Attack Simulation (BAS) assesses the effectiveness of your security controls. Many teams conduct one without the other.
This informative whitepaper delineates six validation surfaces, identifies coverage limitations, and furnishes practitioners with three key evaluative questions for any tool assessment.
-

 Facebook7 months ago
Facebook7 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook8 months ago
Facebook8 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook6 months ago
Facebook6 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook8 months ago
Facebook8 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook6 months ago
Facebook6 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook8 months ago
Facebook8 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook6 months ago
Facebook6 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple8 months ago
Apple8 months agoMeta discontinues Messenger apps for Windows and macOS





























