Security
Uncovering the Methods of Threat Actors in Credit Card Fraud Operations

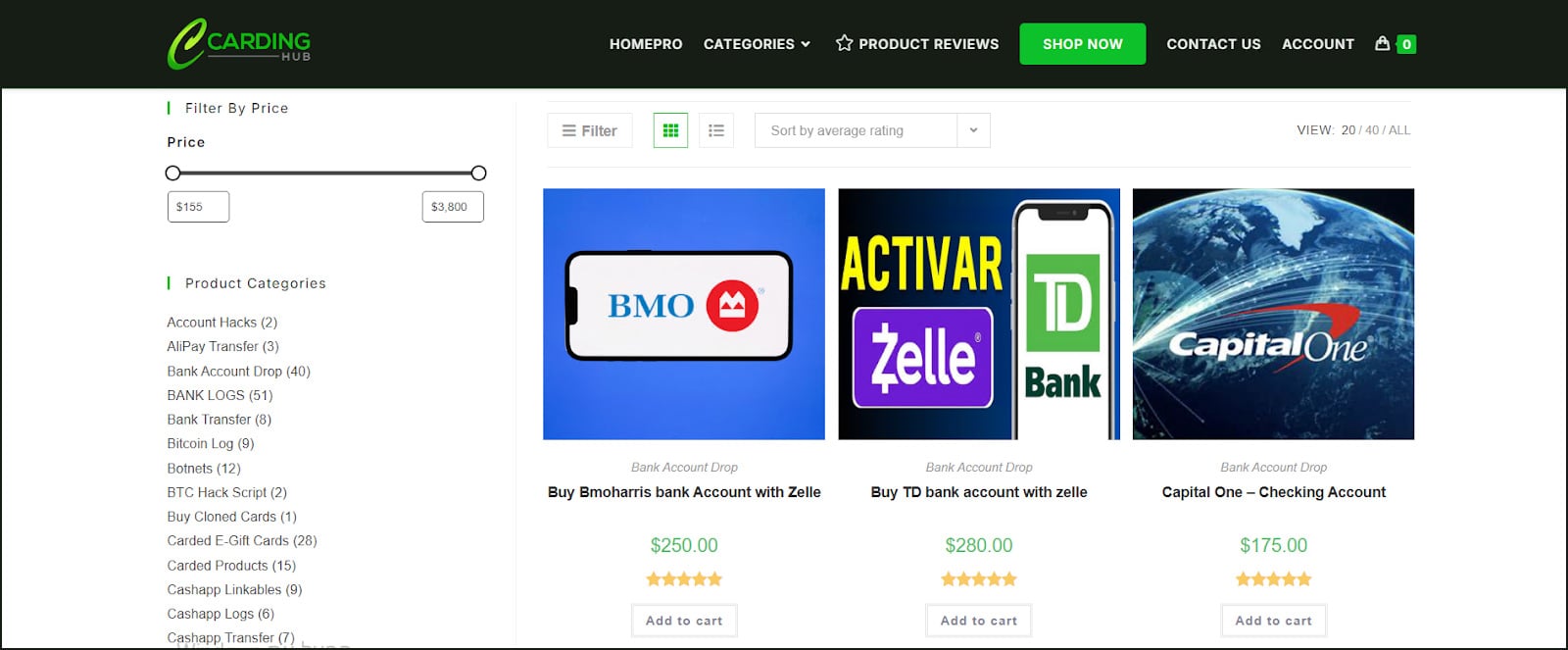
The Intricate World of Stolen Credit Card Data: Navigating the Underground Market
The realm of stolen credit card data has long been a treacherous and volatile ecosystem, where even seasoned actors frequently fall prey to deceptions, exit schemes, and compromised services.
Recent years have witnessed a further destabilization of this environment, propelled by heightened law enforcement scrutiny, internal distrust among criminals, and the rapid turnover of marketplaces. Consequently, threat actors are compelled to adopt more structured approaches to identifying trustworthy suppliers and minimizing risks within their illicit operations.
Unveiled on an underground forum by Flare analysts, a guide sheds light on how threat actors maneuver through the unpredictable terrain of credit card (CC) marketplaces. Titled “The Underground Guide to Legit CC Shops: Cutting Through the Bullshit,” the document offers a systematic overview of how actors strive to mitigate risks in a landscape rife with scams, law enforcement penetrations, and transient operations.
The analysis of the guide transcends mere practical counsel. It delineates a methodology for scrutinizing carding shops, implementing operational security measures, and devising sourcing strategies, effectively delineating the mindset of contemporary fraud actors regarding trust, dependability, and sustainability.
Transitioning from Opportunistic Fraud to Supplier Vetting Discipline
A pivotal aspect of the guide is its repositioning of carding from haphazard fraud to a methodical discipline centered on processes. Rather than fixating on utilizing pilfered cards, the document accentuates the evaluation of suppliers.
This shift mirrors a broader evolution within underground markets, where the paramount risk transcends mere operational lapses to include the perils of being duped by fellow criminals or engaging with compromised infrastructures.
The author underscores that legitimacy is not contingent on branding or visibility but on survivability. In essence, a “genuine” shop is one that endures over time despite law enforcement crackdowns, scams, and internal upheavals.
The narrative aligns with observed trends in underground economies, where the longevity of marketplaces has become increasingly capricious, necessitating actors to embrace continuous authentication practices.
The guide elucidates that the hallmark of a “legitimate” shop is not its branding or uptime but the caliber of the pilfered data it furnishes. Mentions of “fresh bins” (BIN = Bank Identifiable Number) and minimal decline rates unequivocally point to the origins of the data, whether emanating from infostealer incursions, phishing endeavors, or point-of-sale breaches. In this milieu, credibility hinges not on assurances but on consistently delivering functional cards.
Shops that falter in maintaining reliable data streams are swiftly unmasked, while those with consistent access to recent compromises ascend to eminence.
Building Confidence in an Untrustworthy Market
Transparency emerges as a recurring motif in the guide. It underscores the significance of transparent pricing models, real-time stock availability, and efficient support systems encompassing ticketing and escrow services. These attributes closely parallel legitimate e-commerce platforms, underscoring how premier carding shops have embraced business practices geared toward fostering user trust and minimizing friction.
Equally pivotal is the role of community validation. The guide eschews on-site testimonials as unreliable, steering users toward dialogues in exclusive or invite-only forums. This mirrors a broader fragmentation in the underground landscape, where trust is increasingly linked to controlled environments and enduring reputations.
Actors are urged to scrutinize sustained discussion threads and historical presence, eschewing isolated commendations.
The document also unveils a keen awareness of adversarial pressures. The accent on security-centric infrastructure such as mirror domains, DDoS protection, and the absence of tracking mechanisms hints at operators actively warding off both law enforcement surveillance and rival criminal factions.
In essence, these marketplaces function not solely as dissemination platforms but as fortified environments engineered to ensure operational continuity.
The Technical Checklist
Beyond overarching principles, the guide introduces a meticulous vetting protocol that sheds light on how threat actors conduct due diligence. Technical verifications such as domain longevity, WHOIS privacy, and SSL configuration are presented as fundamental prerequisites.
While these checks are relatively straightforward, they underscore an endeavor to subject what has traditionally been a trust-based decision process to structured scrutiny.
The guide also underscores the importance of identifying mirror infrastructure and backup access points, noting that established operations seldom hinge on a solitary domain. This reflects a pragmatic comprehension of the volatility of underground services, where takedowns and disruptions are commonplace. The existence of multiple access points is framed as an indicator of operational sophistication and resilience.
Social intelligence gathering assumes an equally pivotal role. Instead of relying on direct interactions with vendors, users are prompted to dissect forum conversations, track vendor backgrounds, and discern behavioral patterns over time.
Special emphasis is accorded to detecting coordinated endorsement campaigns, such as multiple laudatory reviews originating from freshly minted accounts, a stratagem frequently synonymous with scams.
Operational Security
Another pivotal facet of the guide is its stress on operational security. The recommendations proffered, while couched in the context of carding, closely mirror practices observed across an extensive spectrum of cybercriminal activities. Users are counseled to eschew direct connections, leverage proxy services tailored to target geographies, and compartmentalize their environments through dedicated systems or virtual machines.
The discourse on cryptocurrency deployment is particularly noteworthy. The guide vehemently discourages direct transactions from regulated platforms, instead advocating intermediary wallets and privacy-centric assets like Monero. This echoes an escalating cognizance among threat actors of blockchain analysis capabilities and the hazards associated with traceable financial flows.
Collectively, these OPSEC (operational security) recommendations spotlight a significant shift: actors are no longer relying solely on tools to elude detection but are embracing layered strategies aimed at curtailing exposure across the entire operational chain. This level of discipline intimates that even mid-tier actors are increasingly adopting practices hitherto associated with more advanced threat cohorts.
Scale versus Exclusivity
The guide further categorizes carding shops into distinct operational models, encompassing large automated platforms and smaller, curated vendor cohorts. This segmentation mirrors the diversification of the underground economy, where diverse actors prioritize scale, accessibility, or quality contingent on their objectives.
Automated platforms are delineated as highly efficient realms, often featuring integrated tools and instantaneous purchasing capabilities. These setups bear semblance to bona fide online marketplaces in both structure and functionality, enabling users to promptly procure and assess data at scale.
Conversely, boutique vendor groups underscore exclusivity, superior quality, and restricted access, often banking on invitation-based protocols and enduring relationships.
Commercial Interests and Operational Reality
Despite its methodical approach, the guide is not bereft of bias. The inclusion of a direct endorsement for a specific platform intimates that the author may harbor a vested interest in promoting specific services. This is a prevalent trend in underground circles, where informational content frequently doubles as a conduit for subtle advertising or affiliate undertakings.
Such endorsements warrant circumspection. Nonetheless, they do not necessarily detract from the broader insights proffered by the guide. Instead, they underscore the intricate interplay between information dissemination and commercial motives within cybercriminal ecosystems.
From a defensive standpoint, the guide furnishes invaluable intelligence on how threat actors evaluate risks and make operational decisions. The emphasis on verification, community validation, and layered security bespeaks a level of maturity that complicates traditional disruption endeavors. Rather than hinging on singular vulnerabilities, actors are progressively integrating redundancy and adaptability into their workflows.
Ultimately, the document serves as both a manual and a harbinger. It evinces that the carding ecosystem has metamorphosed into a more structured, cautious, and resilient domain. For defenders, comprehending these dynamics is pivotal in anticipating the continued evolution of these markets and identifying potential avenues for disruption.
How Flare Can Assist
Flare aids organizations in preempting fraud by incessantly monitoring underground forums and marketplaces, unveiling how threat actors procure, vet, and leverage stolen credit card data. This confers early insights into attacker conduct, encompassing their optimization of success rates, trust-building strategies, and adaptability to countermeasures.
By translating this intelligence into actionable intelligence, Flare empowers security teams to pinpoint vulnerabilities, prognosticate fraud campaigns, and thwart attacker workflows, transitioning from reactive responses to proactive, intelligence-driven defenses.
Gain further insights by enrolling in our free trial.
Sponsored and compiled by Flare.
-

 Facebook7 months ago
Facebook7 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook8 months ago
Facebook8 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook6 months ago
Facebook6 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook8 months ago
Facebook8 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook6 months ago
Facebook6 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook8 months ago
Facebook8 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook6 months ago
Facebook6 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple8 months ago
Apple8 months agoMeta discontinues Messenger apps for Windows and macOS




























