Security
Breaking Down Barriers: Overcoming Access Issues in Identity Protection

Over the years, the concept of identity has been pivotal in ensuring workforce security. The traditional belief was that if an organization could accurately ascertain a user’s identity, access could be granted securely.
This model worked well in the past when employees accessed corporate networks using company devices in predictable settings. However, the landscape has shifted, and access patterns have evolved significantly.
Today’s workforce operates in diverse locations, networks, and time zones. Employees seamlessly transition between corporate laptops, personal gadgets, and third-party endpoints.
Access is no longer restricted to a single environment or device, placing a new demand on security teams to support this flexibility without compromising safety or hindering productivity. Yet, the signals used for access decisions have become more complex, fragmented, and less reliable on their own.
Consequently, the burden placed on identity has expanded beyond its initial design. While authentication can confirm a user’s identity, it falls short in assessing the risk associated with access, especially when considering device conditions and context.
The Role of Identity: Defining Who, Not Assessing Risk
Identifying a legitimate user accessing systems from a secure device differs significantly from the same user connecting from an outdated or compromised endpoint. Despite this, many access models continue to treat these scenarios equally, emphasizing identity over device condition.
This approach overlooks the dynamic nature of device risk post-authentication. Endpoints can quickly change status due to configuration modifications, disabled security controls, or delayed updates, leading to a degradation of the risk profile even after access is granted.
When access decisions solely rely on login conditions, trust is maintained even as the underlying risk escalates.
These gaps are most pronounced in access paths outside modern conditional frameworks, such as legacy protocols and remote tools. In these instances, access decisions are often made with limited context, extending trust beyond justified levels.
Attackers exploit these vulnerabilities by leveraging misplaced trust, circumventing authentication, abusing compromised endpoints, or bypassing multi-factor authentication.
Ultimately, it is easier for malicious actors to gain access through a valid identity on an unsecured device, bypassing modern security controls.
Verizon’s Data Breach Investigation Report highlighted that stolen credentials are implicated in 44.7% of breaches.
Secure Active Directory effortlessly with compliant password policies, blocking over 4 billion compromised passwords, enhancing security, and reducing support challenges!
Try it for free
Challenges with Zero Trust Implementation
While Zero Trust is widely acknowledged as a fundamental security principle, its consistent application across workforce access remains a challenge. Although identity controls have improved, progress often stalls at the device level, especially in non-browser-based access paths inheriting trust by default.
Establishing trust in devices introduces complexities that identity alone cannot address. Unmanaged and personal devices pose difficulties in consistent assessment, compliance checks are typically static, and enforcement varies based on access initiation methods.
These issues are compounded when identity and endpoint signals are managed by separate tools not designed to collaborate, leading to fragmented visibility and inconsistent decision-making.
Over time, access policies can become rigid and static, opening avenues for identity exploitation. Without continuous checks post-access, traditional controls struggle to detect and respond to malicious activities promptly.
Transitioning from Identity-Centric to Continuous Access Verification
To address the limitations of static, identity-focused access controls, mechanisms need to remain effective post-authentication and adapt to changing conditions.
Solutions like Infinipoint embody this approach by extending trust decisions beyond identity and enforcing security as conditions evolve.
The following strategies aim to address common access vulnerabilities without disrupting daily operations:
- Continuous Verification of User and Device: By tying access to a trusted endpoint rather than solely relying on identity, this approach reduces the impact of stolen credentials and authentication bypass techniques.
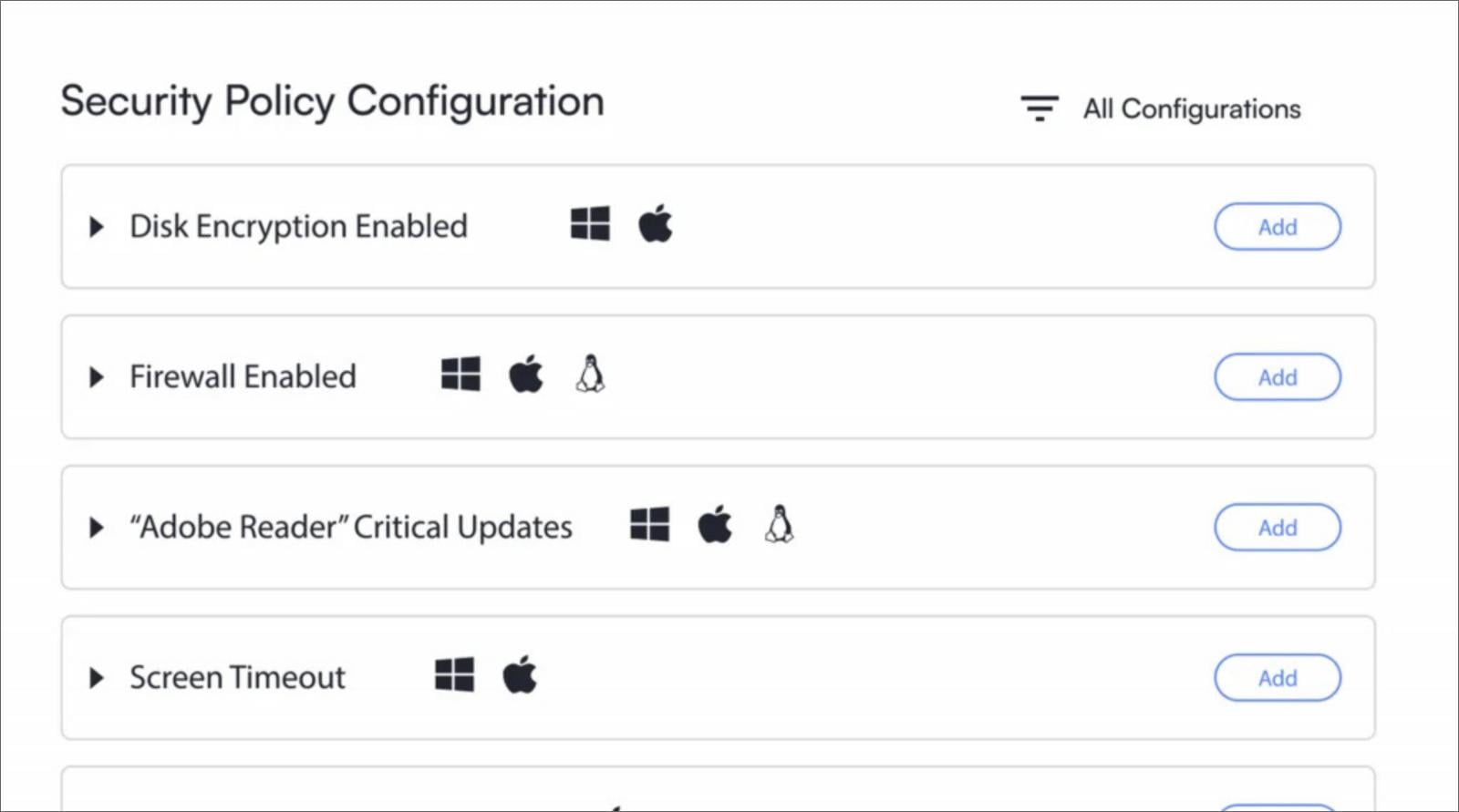
- Implementation of Device-Based Access Controls: Enrolling approved hardware, restricting the number and types of devices per user, and distinguishing between corporate, personal, and third-party endpoints can prevent unauthorized access from untrusted devices.
- Enforcement of Security with Minimal Disruption: Proportionate enforcement enables organizations to mitigate risks without unnecessarily interrupting legitimate activities. This includes conditional restrictions and grace periods to allow users to rectify issues while upholding security standards.
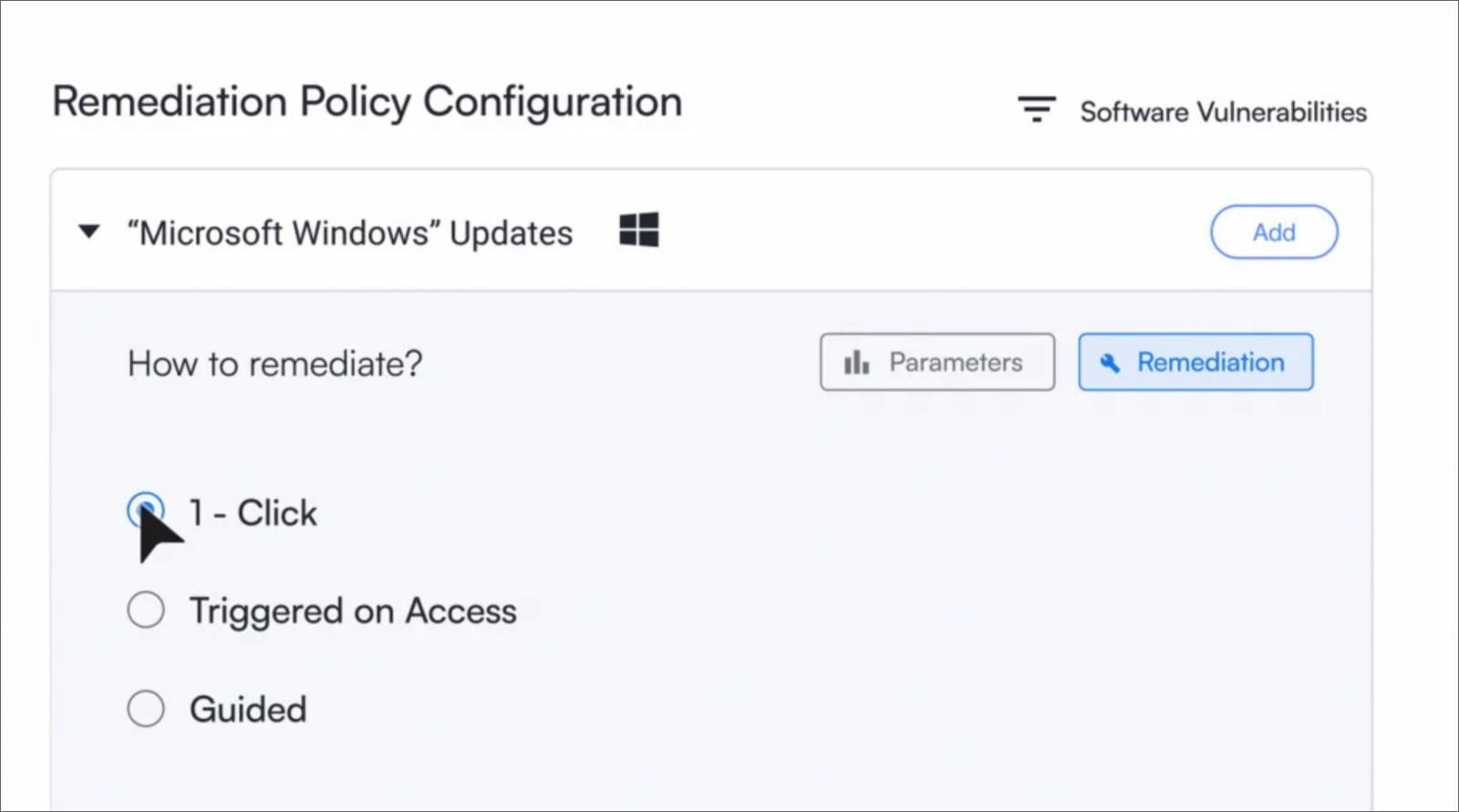
- Facilitating Self-Service Remediation: Offering self-guided remediation steps, such as enabling encryption or updating operating systems with a single click, expedites trust restoration, reduces support tickets, and eases the burden on IT teams while maintaining security protocols.
Specops, the Identity and Access Management division of Outpost24, offers these comprehensive controls through Infinipoint, enabling a Zero Trust workforce access model that verifies users and devices at every point of access, continuously throughout each session across various platforms.
Consult with a Specops expert to implement device-centric Zero Trust access beyond identity.
This content is sponsored and authored by Specops Software.
-

 Facebook7 months ago
Facebook7 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook8 months ago
Facebook8 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook6 months ago
Facebook6 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook8 months ago
Facebook8 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook6 months ago
Facebook6 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook8 months ago
Facebook8 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook6 months ago
Facebook6 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple7 months ago
Apple7 months agoMeta discontinues Messenger apps for Windows and macOS































