Security
Enhanced Security Measures: Google Chrome’s Infostealer Protection for Session Cookie Theft

Google Chrome Enhances Security Against Info-Stealing Malware
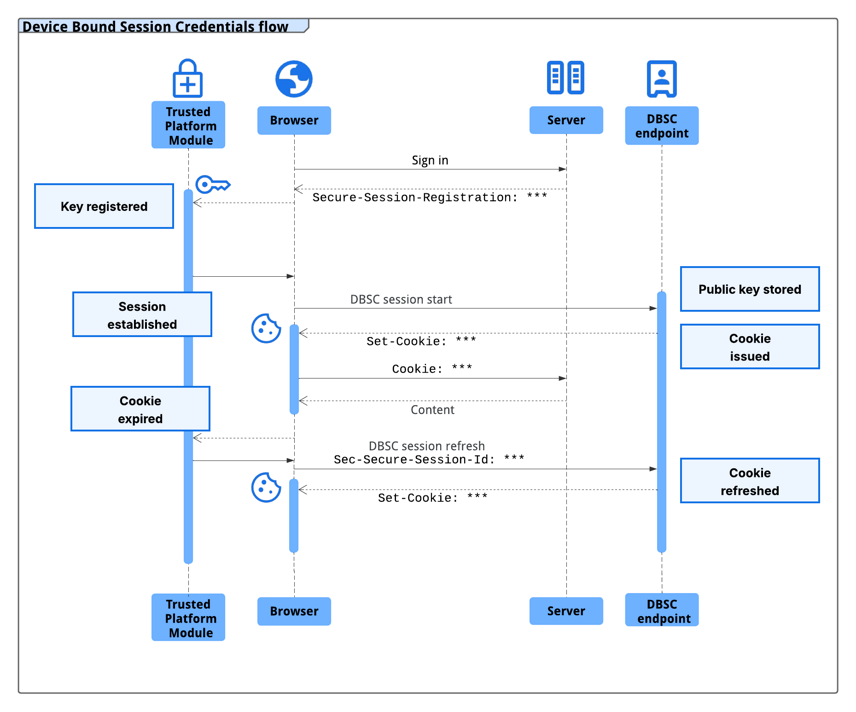
Google has recently introduced Device Bound Session Credentials (DBSC) protection in Chrome version 146 for Windows. This update aims to prevent info-stealing malware from collecting session cookies, thereby enhancing user security.
While Windows users can already benefit from this new security feature, macOS users can expect it in a future Chrome release, although the specific date has not been announced yet.
The announcement of this new protection was made in 2024, and it operates by linking a user’s session to their hardware, such as the Trusted Platform Module (TPM) on Windows and the Secure Enclave on macOS.
By generating unique public/private keys for encrypting sensitive data through the security chip, Chrome ensures that these keys cannot be exported from the device. This approach effectively prevents attackers from using stolen session data.
According to Google, the issuance of new session cookies is dependent on Chrome proving possession of the corresponding private key to the server. Without this key, any stolen session cookie becomes unusable almost immediately.
source: Google
A session cookie functions as an authentication token created server-side based on user credentials. Threat actors often use specialized malware known as infostealer to collect these session cookies and gain unauthorized access to user accounts.
The DBSC protocol is designed to be private, with each session backed by a unique key. This prevents websites from tracking user activity across different sessions on the same device.
In collaboration with web platforms like Okta, Google observed a decrease in session theft events during a year of testing the early version of DBSC. The protocol, developed in partnership with Microsoft, is aimed to become an open web standard.
Websites can adopt more secure, hardware-bound sessions by implementing dedicated registration and refresh endpoints to their backend systems without compromising compatibility with existing frontends.
For web developers interested in implementing DBSC, Google provides a comprehensive guide with specifications available on the World Wide Web Consortium (W3C) website and an explainer on GitHub.

Automated pentesting proves the path exists. BAS proves whether your controls stop it. Most teams run one without the other.
This whitepaper maps six validation surfaces, shows where coverage ends, and provides practitioners with three diagnostic questions for any tool evaluation.
-

 Facebook7 months ago
Facebook7 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook8 months ago
Facebook8 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook6 months ago
Facebook6 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook8 months ago
Facebook8 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook6 months ago
Facebook6 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook8 months ago
Facebook8 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook6 months ago
Facebook6 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple7 months ago
Apple7 months agoMeta discontinues Messenger apps for Windows and macOS