Security
Urgent Alert: Nginx UI Vulnerability Exploited in the Wild

An ongoing exploitation of a critical vulnerability in Nginx UI, featuring Model Context Protocol (MCP) support, has been detected, enabling unauthorized individuals to take over servers without authentication.
The identified flaw, designated as CVE-2026-33032, is a result of nginx-ui leaving the ‘/mcp_message’ endpoint vulnerable, allowing remote attackers to execute privileged MCP actions without the need for credentials.
Due to the nature of these actions, which involve the manipulation of nginx configuration files, a single unauthenticated request has the potential to alter server configurations and essentially gain control of the web server.

According to the description provided by the National Institute of Standards and Technology (NIST) in the National Vulnerability Database (NVD), “any network attacker can invoke all MCP tools without authentication, including restarting nginx, creating/modifying/deleting nginx configuration files, and triggering automatic config reloads – achieving complete nginx service takeover.”
The vulnerability was addressed by NGINX in version 2.3.4 on March 15, following its report by researchers from the AI workflow security company, Pluto Security AI. However, the details of the vulnerability, including technical aspects and a proof-of-concept (PoC) exploit, surfaced at the end of the month.
In a recent CVE Landscape report, threat intelligence firm Recorded Future highlighted that CVE-2026-33032 is currently being actively exploited.
Nginx UI serves as a web-based management interface for the Nginx web server and boasts considerable popularity, with over 11,000 stars on GitHub and 430,000 Docker pulls.
Based on internet scans conducted by Pluto Security using the Shodan engine, there are approximately 2,600 publicly exposed instances that may be vulnerable to attacks. These instances are primarily located in China, the United States, Indonesia, Germany, and Hong Kong.
In a recent report, Yotam Perkal from Pluto Security stated that exploitation of the vulnerability only requires network access and involves establishing an SSE connection, initiating an MCP session, and utilizing the returned ‘sessionID’ to send requests to the ‘/mcp_message’ endpoint.
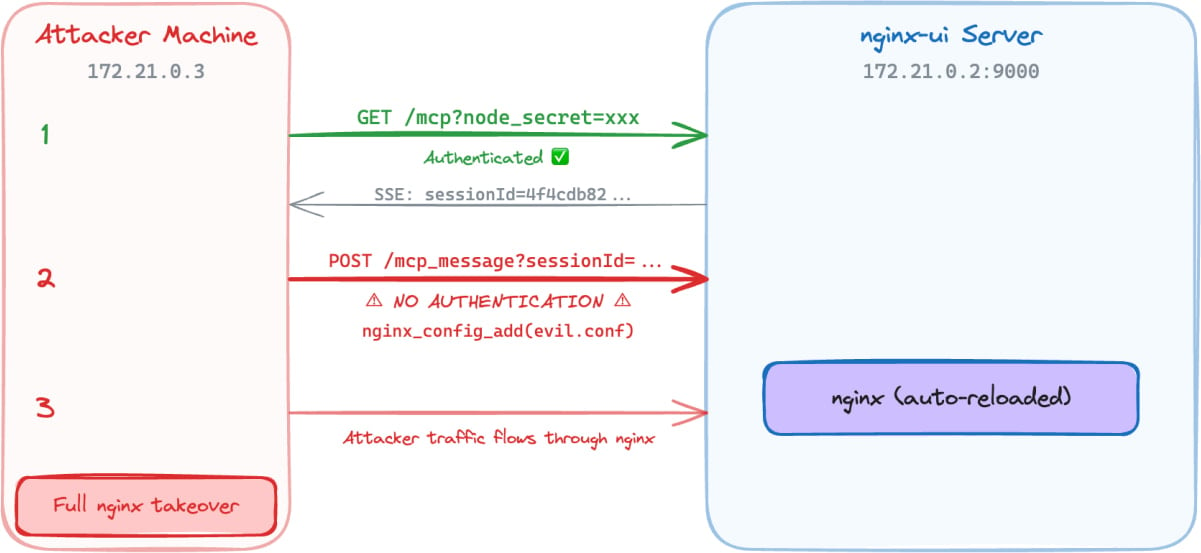
Source: Pluto Security
Subsequently, attackers can leverage MCP tools without authentication and execute various actions, such as:
- Connecting to the target nginx-ui instance
- Sending requests without any authentication headers
- Gaining access to all 12 MCP tools (including 7 destructive ones)
- Reading nginx configuration files and extracting them
- Injecting a new nginx server block with malicious configurations
- Triggering automatic nginx reloads
A demonstration by Pluto Security illustrates how an attacker can utilize the unauthenticated MCP message endpoint to perform privileged nginx management actions, inject configurations, and ultimately seize control of the nginx server without authentication.
Given the active exploitation status and the existence of public PoCs, system administrators are strongly advised to promptly apply the available security updates. The most recent secure version of nginx-ui, version 2.3.6, was released last week.

Automated pentesting proves the path exists. BAS proves whether your controls stop it. Most teams run one without the other.
This whitepaper maps six validation surfaces, shows where coverage ends, and provides practitioners with three diagnostic questions for any tool evaluation.
-

 Facebook7 months ago
Facebook7 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook8 months ago
Facebook8 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook6 months ago
Facebook6 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook8 months ago
Facebook8 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook6 months ago
Facebook6 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook8 months ago
Facebook8 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook6 months ago
Facebook6 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple7 months ago
Apple7 months agoMeta discontinues Messenger apps for Windows and macOS































