Security
US Citizens Involved in North Korean IT Worker ‘Laptop Farm’ Operation Sentenced to Prison

US Nationals Imprisoned for Assisting North Korean IT Workers in Identity Theft Scheme
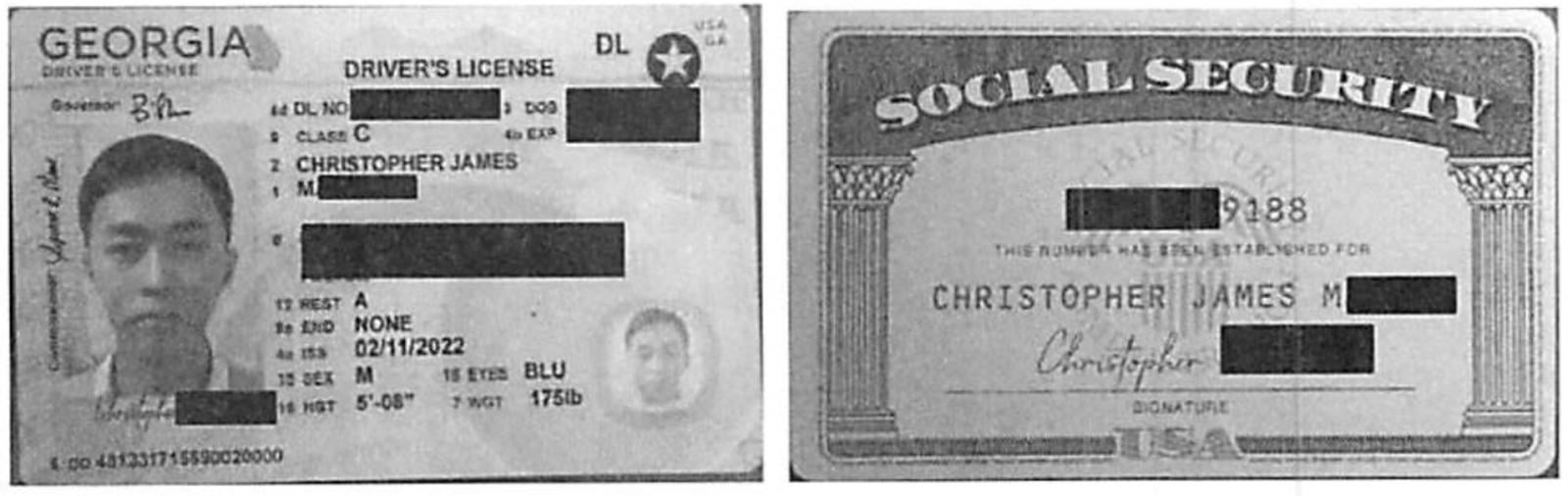
Two individuals, Kejia Wang and Zhenxing Wang, have been sentenced to prison for their involvement in a scheme that saw North Korean IT workers posing as US residents to secure employment in over 100 American companies, including several Fortune 500 firms.
Kejia Wang, aged 42, and Zhenxing Wang, aged 39, were charged in June 2025 as part of a coordinated law enforcement operation against the fundraising activities of the Democratic People’s Republic of Korea (DPRK) government, led by the US Department of Justice (DoJ).
Court documents reveal that between 2021 and October 2024, the two individuals generated over $5 million in illicit revenue for the DPRK government, causing an estimated $3 million in financial losses to companies that unknowingly hired North Korean workers using the identities of more than 80 US citizens.

The duo established financial accounts, fake websites, and multiple shell companies like Tony WKJ LLC, Hopana Tech LLC, and Independent Lab LLC to create an illusion of association between North Korean workers and legitimate US businesses, thereby collecting payments.
Zhenxing Wang went a step further by hosting company-issued laptops in various locations across the US, enabling remote North Korean IT workers to access company networks without raising suspicion.
Assistant Attorney General for National Security, John A. Eisenberg, condemned the defendants’ actions, stating that they had aided North Korean actors in a fraudulent scheme that compromised US national security by placing North Korean IT workers within American companies.
Nine other defendants implicated in the same scheme are still at large, with the US State Department offering a reward of up to $5 million for information leading to their apprehension to disrupt illicit activities supporting North Korea’s weapons of mass destruction program.
Kejia Wang and Zhenxing Wang were sentenced to 108 months and 92 months in prison, respectively, after pleading guilty to their roles in the scheme. In addition, Ukrainian national Oleksandr Didenko received a five-year prison sentence for aiding DPRK IT workers in infiltrating US companies using stolen identities.
The FBI has issued warnings about North Korean threat actors impersonating US-based IT staff since 2023, highlighting the DPRK’s extensive network of IT workers utilizing stolen identities to secure employment in American companies.

Automated pentesting proves the path exists. BAS proves whether your controls stop it. Most teams run one without the other.
This whitepaper maps six validation surfaces, shows where coverage ends, and provides practitioners with three diagnostic questions for any tool evaluation.
-

 Facebook7 months ago
Facebook7 months agoEU Takes Action Against Instagram and Facebook for Violating Illegal Content Rules
-

 Facebook8 months ago
Facebook8 months agoWarning: Facebook Creators Face Monetization Loss for Stealing and Reposting Videos
-

 Facebook6 months ago
Facebook6 months agoFacebook’s New Look: A Blend of Instagram’s Style
-

 Facebook8 months ago
Facebook8 months agoFacebook Compliance: ICE-tracking Page Removed After US Government Intervention
-

 Facebook6 months ago
Facebook6 months agoFacebook and Instagram to Reduce Personalized Ads for European Users
-

 Facebook8 months ago
Facebook8 months agoInstaDub: Meta’s AI Translation Tool for Instagram Videos
-

 Facebook6 months ago
Facebook6 months agoReclaim Your Account: Facebook and Instagram Launch New Hub for Account Recovery
-

 Apple7 months ago
Apple7 months agoMeta discontinues Messenger apps for Windows and macOS